Examine the evidence of exploitability
The Evidence section provides supporting proof of the existence and exploitation of a particular vulnerability. To go there, enter your group, click on a type of vulnerability and select Evidence from the tabs. In this section, Fluid Attacks' security analysts present evidence in pictures (with .png and .jpg extensions) and videos (with WebM extension), helping you identify this type of vulnerability in your system when reported for the first time. The evidence presented may change whenever a reattack is performed to check the presence of this type of vulnerability.
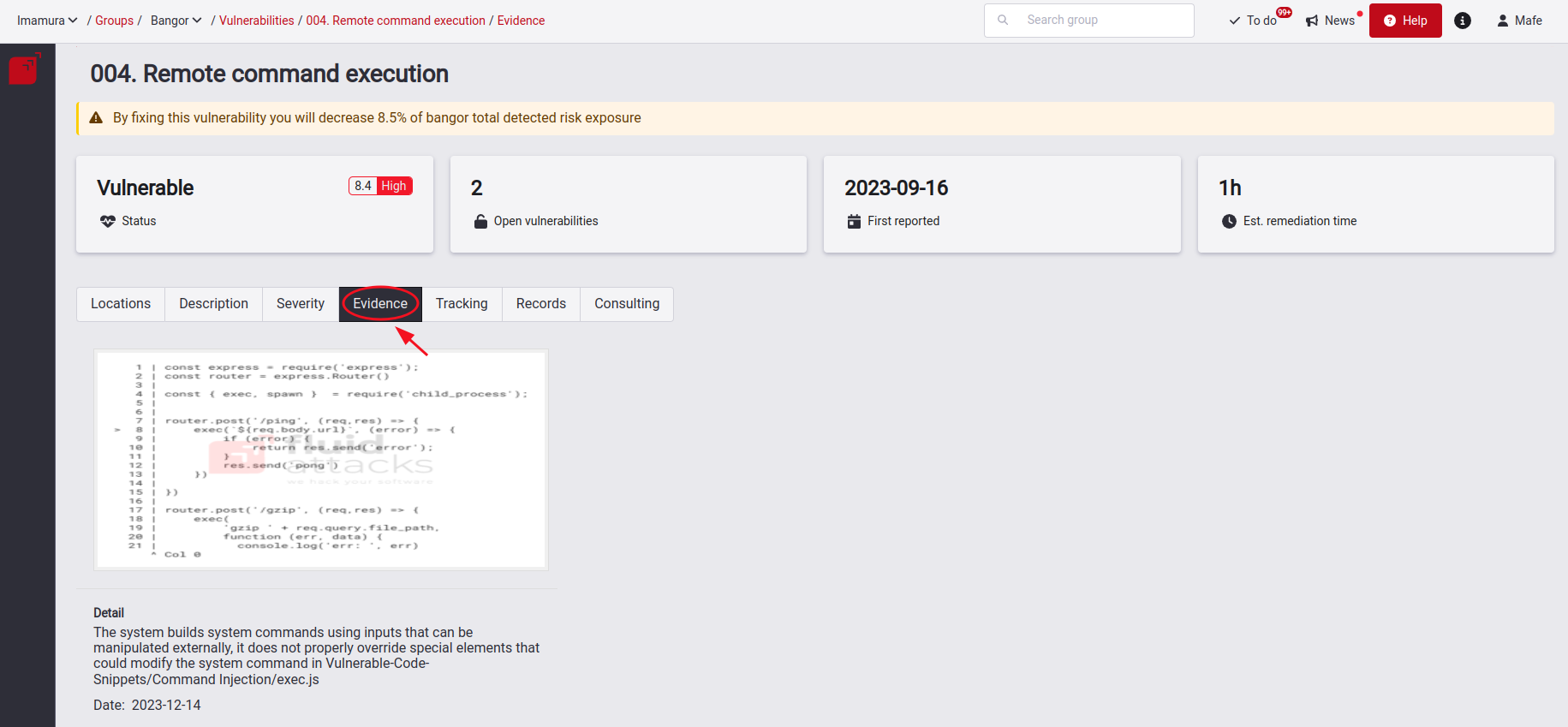
The number of evidence items is limited to seven. These items can be updated according to the analyst's or your request in the Consulting section.

Free trial
Search for vulnerabilities in your apps for free with Fluid Attacks' automated security testing! Start your 21-day free trial and discover the benefits of the Continuous Hacking Essential plan. If you prefer the Advanced plan, which includes the expertise of Fluid Attacks' hacking team, fill out this contact form.