Encryption in transit
Last updated: Mar 16, 2026
All our applications and services have industry-standard encryption in transit.
- The Fluid Attacks domain uses the latest TLSv1.3 cryptographic protocol for maximum protection of data in transit.
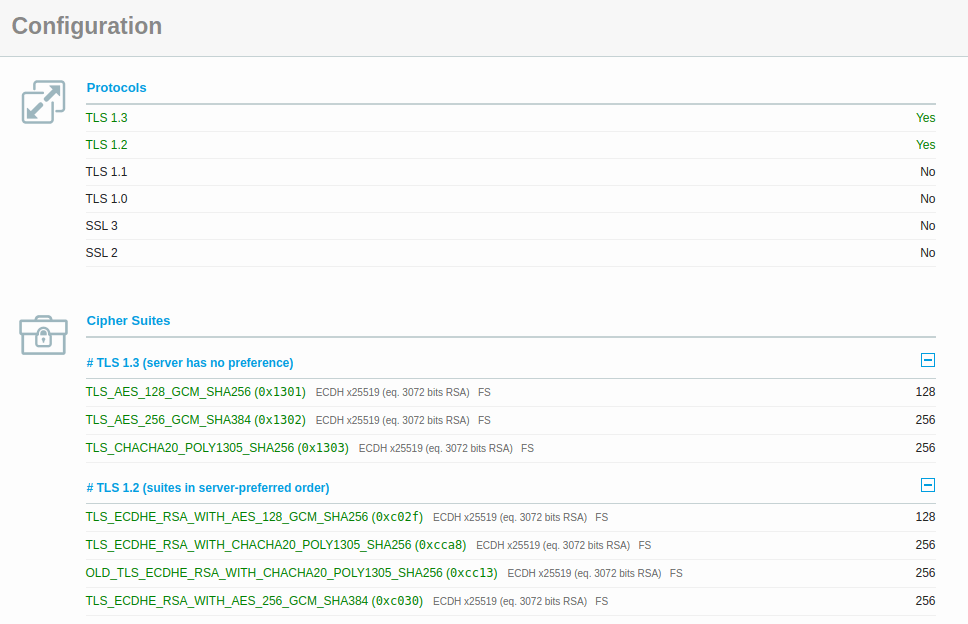
SSL configuration (retrieved from [SSL Labs](https://www.ssllabs.com))
- Digital certificates for Fluid Attacks are renewed every 30 days in order to minimize leaks.
- We use the HSTS policy to ensure that every connection to our domain goes through HTTPS.
- We demand all connections to support at least TLSv1.2.
- Our platform's database uses TLSv1.2 for the protection of data in transit.
- We possess fully dedicated network channels with some of our biggest clients, allowing us to isolate all unwanted traffic. This is particularly useful for running secure dynamic application hacking.
- For the rest of our clients, we use fully encrypted VPNs.
- We maintain an SSL A+ score from SSL Labs. An updated report can be found in Fluid Attacks' profile.
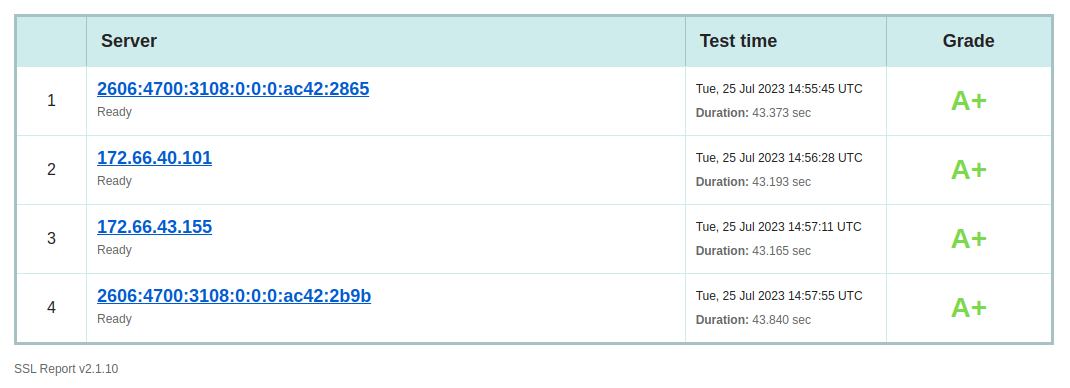
SSL report (retrieved from [SSL Labs](https://www.ssllabs.com))
Requirements
- 092. Use externally signed certificates
- 147. Use pre-existent mechanisms
- 181. Transmit data using secure protocols
- 336. Disable insecure TLS versions
Other confidentiality measures
Encryption at rest
Fluid Attacks protects sensitive data using AES-256 GCM encryption, KMS-managed secrets, and full-disk encryption (BitLocker, LUKS, FileVault) in all devices.
No personal gain
Fluid Attacks prohibits the exploitation of discovered vulnerabilities for personal gain. It ensures confidentiality and integrity in all engagements.