Cloud
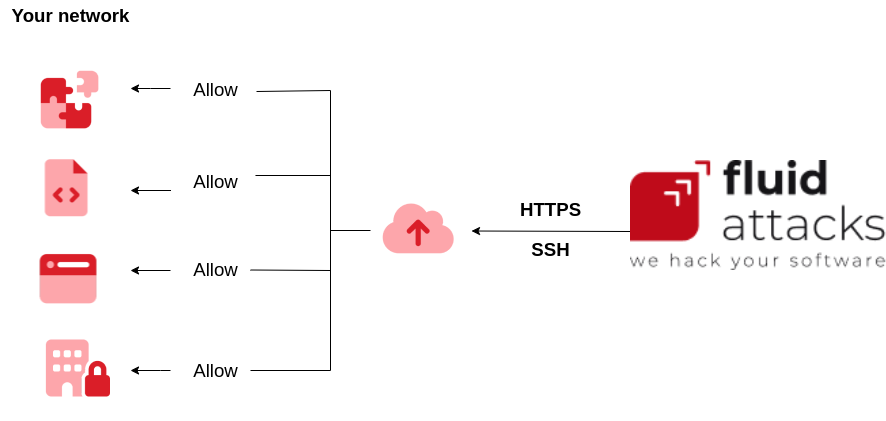
Security in the cloud connection is guaranteed through the use of encryption and strong authentication, aligning it with the high-security standards provided by the different connection protocols, thus ensuring that the interaction with the cloud resources is smooth and fast, maintaining a high level of protection in line with the best security practices.
High-level-architecture
The high-level architecture for Internet connectivity is based on a comprehensive approach that ensures both security and efficiency in data exchange. An overview is presented here:
-
Fluid attacks are connected through various devices, such as computers, mobile devices, or workstations.
-
The connection is initiated through Internet Service Providers (ISPs), the first point of entry to the global network.
-
User data travels through the Internet infrastructure, using routing protocols to navigate to its destination efficiently.
-
Routers and servers along the way facilitate the seamless data transfer across interconnected global networks.
-
The security layer is reinforced by protocols such as HTTPS (Hypertext Transfer Protocol Secure) for secure data transmission on the web.
-
SSH (Secure Shell) is implemented for a secure and encrypted connection for more advanced and remote operations, especially useful for system administration and file transfer on the web.
-
The data finally reaches the desired servers and resources, including web servers, databases, and cloud applications.
-
Cloud infrastructure can be crucial, enabling fast access and scalability according to user needs.
-
The server responds to the user over the same secure connection, completing the interaction cycle.

Minimum requirements
At a minimum, your resources are required to have an internet connection.
Service limitations
As a limitation, it is perceived to depend on the internet connection.
Authentication
The authentication mechanisms available for this method are as follows:
| OAuth | SSH | HTTPS |
|---|---|---|
| ✅ | ✅ | ✅ |