Monitoring
Last updated: Feb 18, 2026
General
For general monitoring, we use different types of tools and services that help us to be aware of issues in our stack.
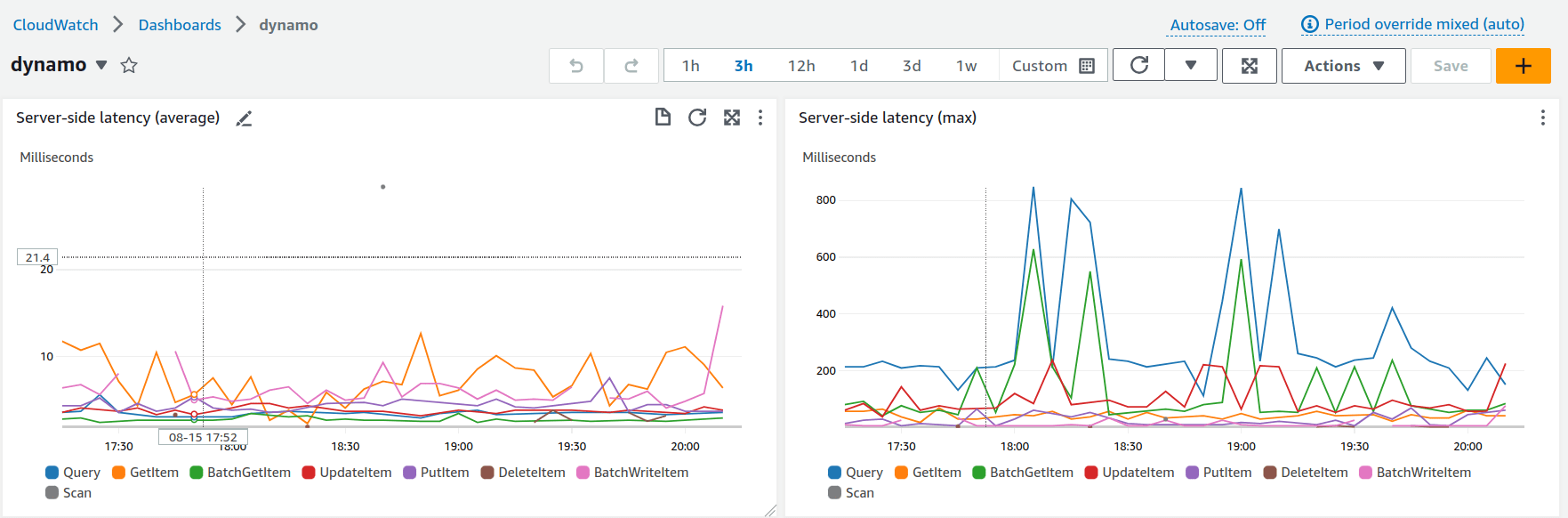
- We monitor AWS infrastructure with CloudWatch.
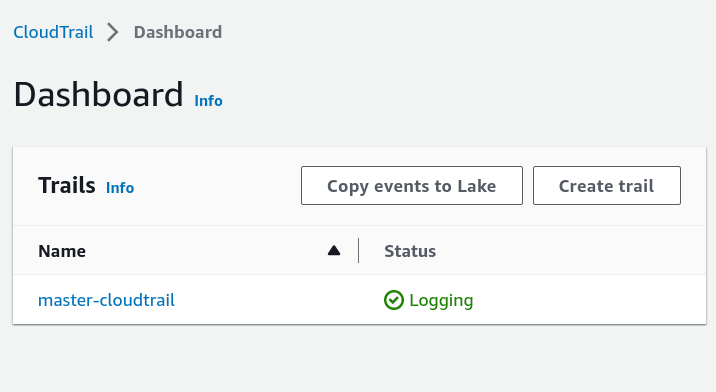
- For management purposes on AWS accounts, we register events related to them using CloudTrail.
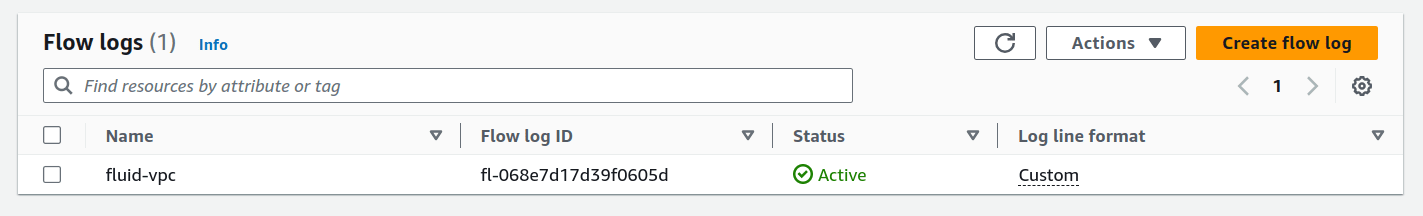
- With VPC Flow Logs, we can capture ingoing and outgoing IP traffic information from network interfaces in our VPC.
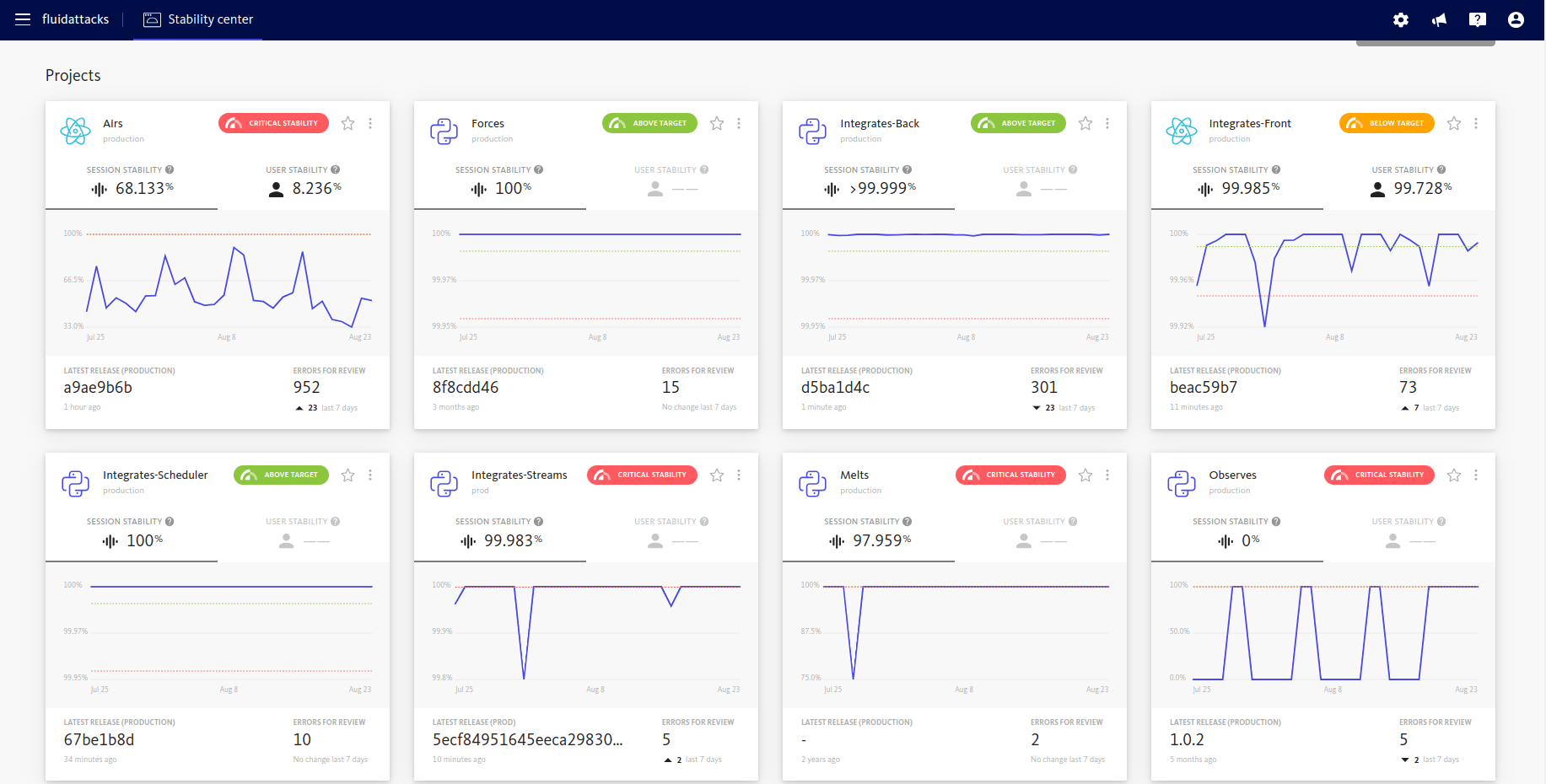
- BugSnag is a tool we use for error monitoring, tracking and alerting.
Threat detection
For threat detection purposes, we adopted Amazon GuardDuty. It continuously monitors for malicious activity and unauthorized behavior to protect AWS accounts, Amazon Elastic Compute Cloud (EC2) workloads, container applications, and data stored in Amazon Simple Storage Service (S3).
GuarDuty uses machine learning, anomaly detection, network monitoring, and malicious file discovery for threat and intrusion detection tasks.
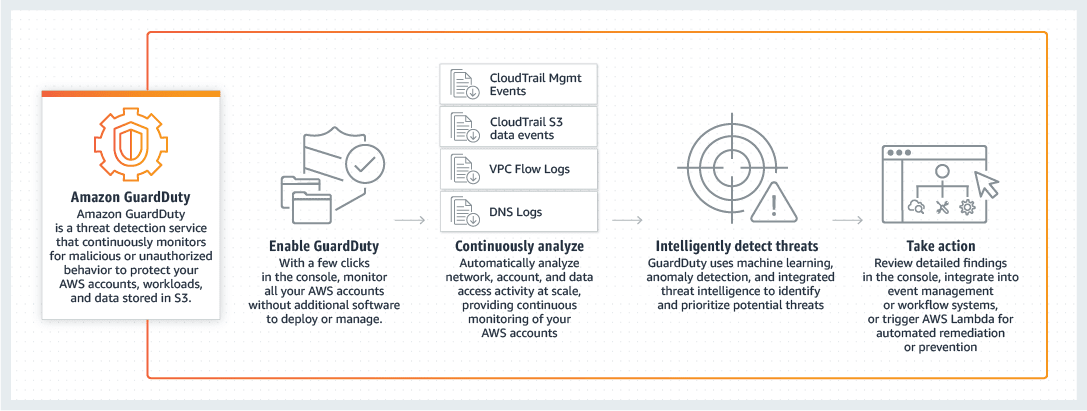
It is capable of analyzing tens of billions of events across multiple AWS data sources, such as AWS CloudTrail event logs, Amazon Virtual Private Cloud (VPC) Flow Logs, Amazon Elastic Kubernetes Service (EKS) audit and system-level logs, and DNS query logs.
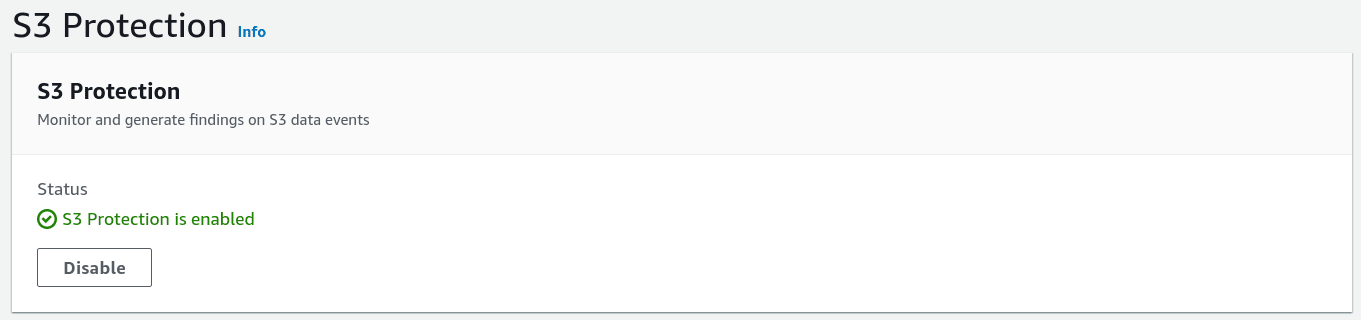
S3 Protection
S3 Protection is a feature offered by Amazon GuardDuty that enhances the monitoring capabilities for data stored in Amazon S3 buckets. By default, GuardDuty monitors bucket-level API operations related to S3 resources. However, with S3 Protection enabled, GuardDuty expands its monitoring to include object-level API operations within S3 buckets. This means it can detect suspicious or potentially malicious activities at a more granular level.
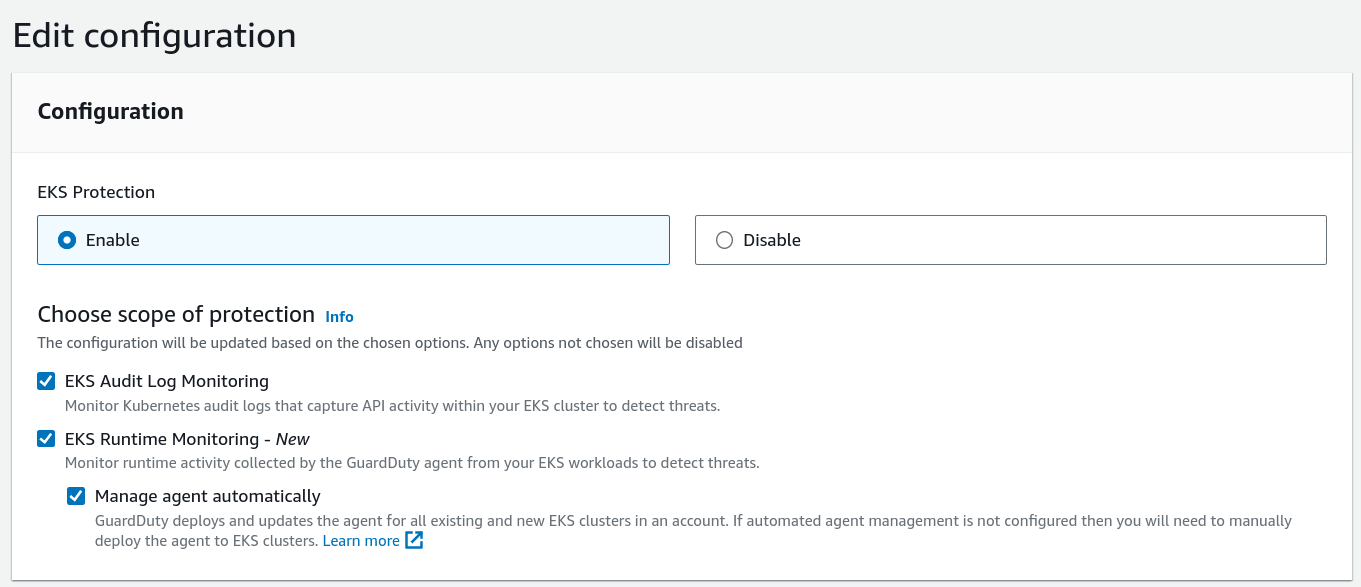
EKS Protection
EKS Protection in Amazon GuardDuty offers threat detection coverage for Amazon Elastic Kubernetes Service (Amazon EKS) clusters in your AWS environment. It includes two key components: EKS Audit Log Monitoring and EKS Runtime Monitoring.
EKS Audit Log Monitoring focuses on detecting suspicious activities within EKS clusters by analyzing Kubernetes audit logs. These logs capture a sequential record of actions performed by users, applications using the Kubernetes API, and the control plane.
EKS Runtime Monitoring provides real-time threat detection for Amazon EKS nodes and containers in your AWS environment. By leveraging the Amazon EKS add-on GuardDuty security agent, it monitors and analyzes runtime events within your EKS clusters, helping to identify potential security threats.
By configuring your accounts with both EKS Audit Log Monitoring and EKS Runtime Monitoring, you can achieve comprehensive EKS Protection. This setup enables monitoring at the cluster control plane level and extends down to the individual pod or container operating system level, providing optimal security coverage for your EKS environment.
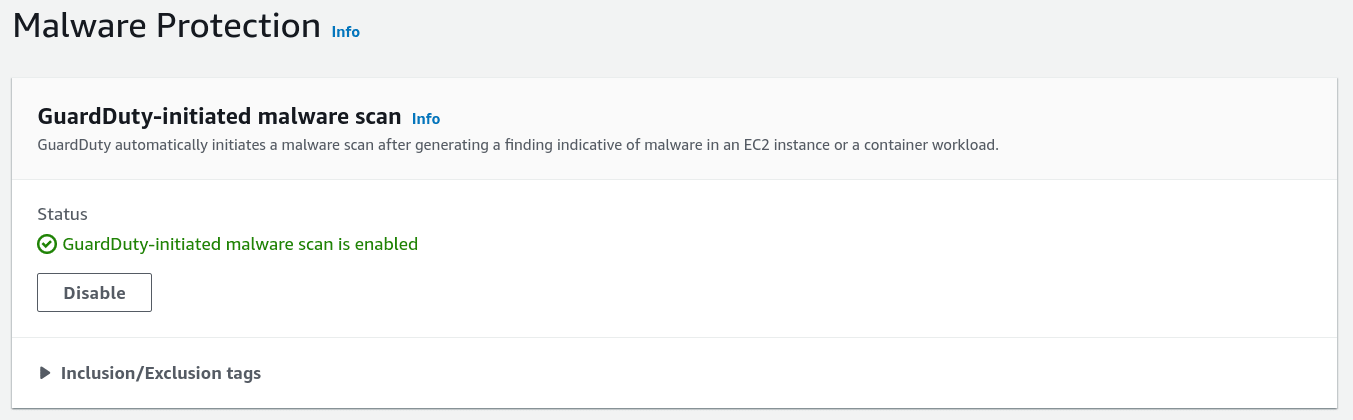
Malware protection
Malware Protection in Amazon GuardDuty is a feature designed to identify potential malware presence in Amazon EC2 instances and container workloads within your AWS account. It performs scans on the Amazon Elastic Block Store (EBS) volumes attached to these instances or workloads.
There are two types of scans offered:
- GuardDuty-initiated malware scan: This scan is initiated by GuardDuty on a periodic basis. It automatically scans the EBS volumes associated with your EC2 instances and container workloads to detect any signs of malware.
- On-demand malware scan: With this option, you can manually trigger a malware scan for specific EBS volumes. It allows you to initiate a scan whenever needed, providing flexibility in scanning resources on demand.
By leveraging these scanning capabilities, Malware Protection helps you proactively detect the potential presence of malware in your EC2 instances and container workloads.
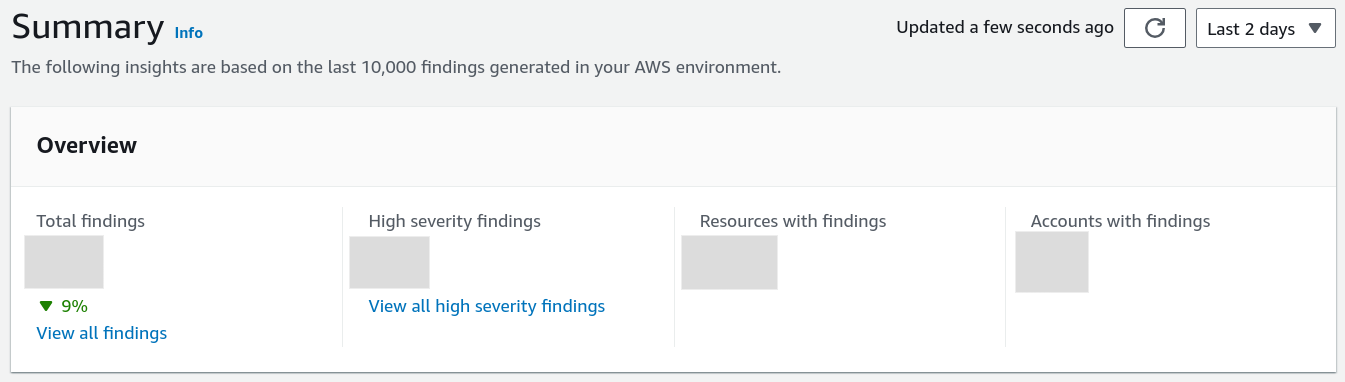
AWS GuardDuty summary
While GuardDuty generates detailed findings and insights based on the last 10,000 events, it does not directly generate predefined reports summarizing these findings. However, by analyzing the generated findings, you can gain valuable insights into common attack vectors, suspicious user behavior, unauthorized access attempts, data exfiltration attempts, malicious IP addresses, vulnerable EC2 instances, anomalous network traffic, cryptocurrency mining activity, suspicious DNS activity, and policy violations. Regularly reviewing and addressing these findings enables you to proactively strengthen your security measures and protect your AWS resources against potential threats and attacks.
AWS Inspector
Amazon Inspector is a comprehensive automated security assessment service designed to evaluate AWS workloads for software vulnerabilities and potential unintended network exposure. This tool assists Fluid Attacks in identifying and resolving security issues within the AWS environment, covering areas such as EC2 instances, container images, and Lambda functions.
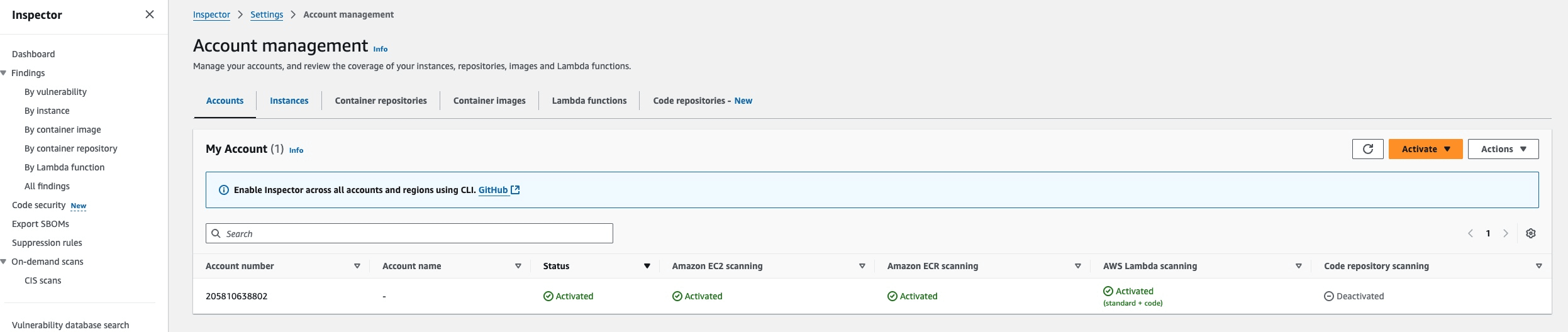
The AWS Inspector alert review process is managed by Fluid Attacks' engineering team. Each critical patch identified thanks to this service must be installed within 30 days.
Datadog overview
Log management
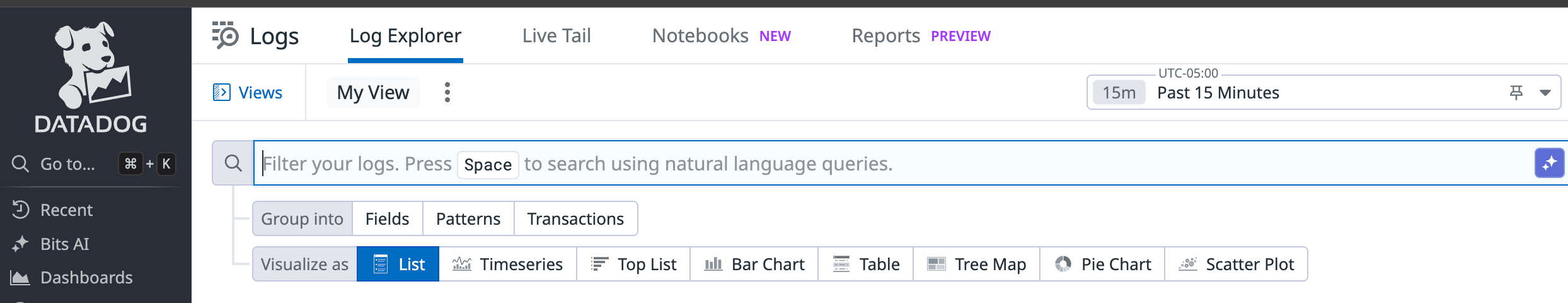
Datadog Log Management enables us to collect, monitor, manage, and analyze large volumes of logs as well as unify metrics and traces. The platform provides comprehensive log analytics with several key functionalities:
Advanced log analytics and search
- Frequently, logs have more contextual information, and by adding custom facets as we need them, we are able to very quickly break things down in new dimensions and find issues
- Real-time log exploration through the Log Explorer interface
- Full-text search capabilities across all ingested logs
- Custom filtering and faceting for dimensional analysis
Log-to-metric and trace correlation
- Correlate our logs and metrics to gain context of an issue and map it throughout our service.
- The correlation between Datadog APM and Datadog Log Management is improved by the injection of trace IDs, span IDs, env, service, and version as attributes in logs.
- Datadog automatically brings together all the logs for a given request and links them seamlessly to tracing data from that same request.
Distributed tracing capabilities
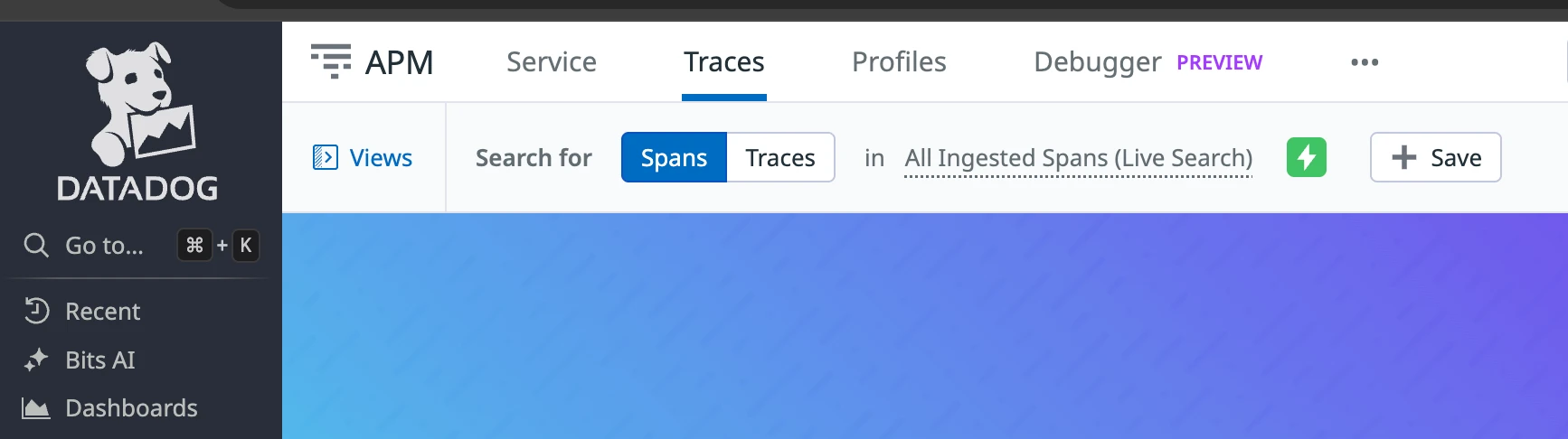
- End-to-end request tracking: Datadog APM (Application Performance Monitoring) provides complete visibility into distributed transactions across microservices and cloud infrastructure.
- Performance analysis: Identify bottlenecks, latency issues, and performance degradation with detailed trace analytics.
- Service dependencies mapping: Automatically discover and visualize service-to-service communications and dependencies.
- Error tracking and root cause analysis: Link errors in traces directly to corresponding logs and metrics for faster troubleshooting.
- Trace search and analytics: Query and analyze traces using tags, facets, and custom attributes for deep performance insights.
- Integration with logs and metrics: Seamlessly pivot between traces, logs, and metrics to understand the full context of application behavior.
Cloud SIEM capabilities
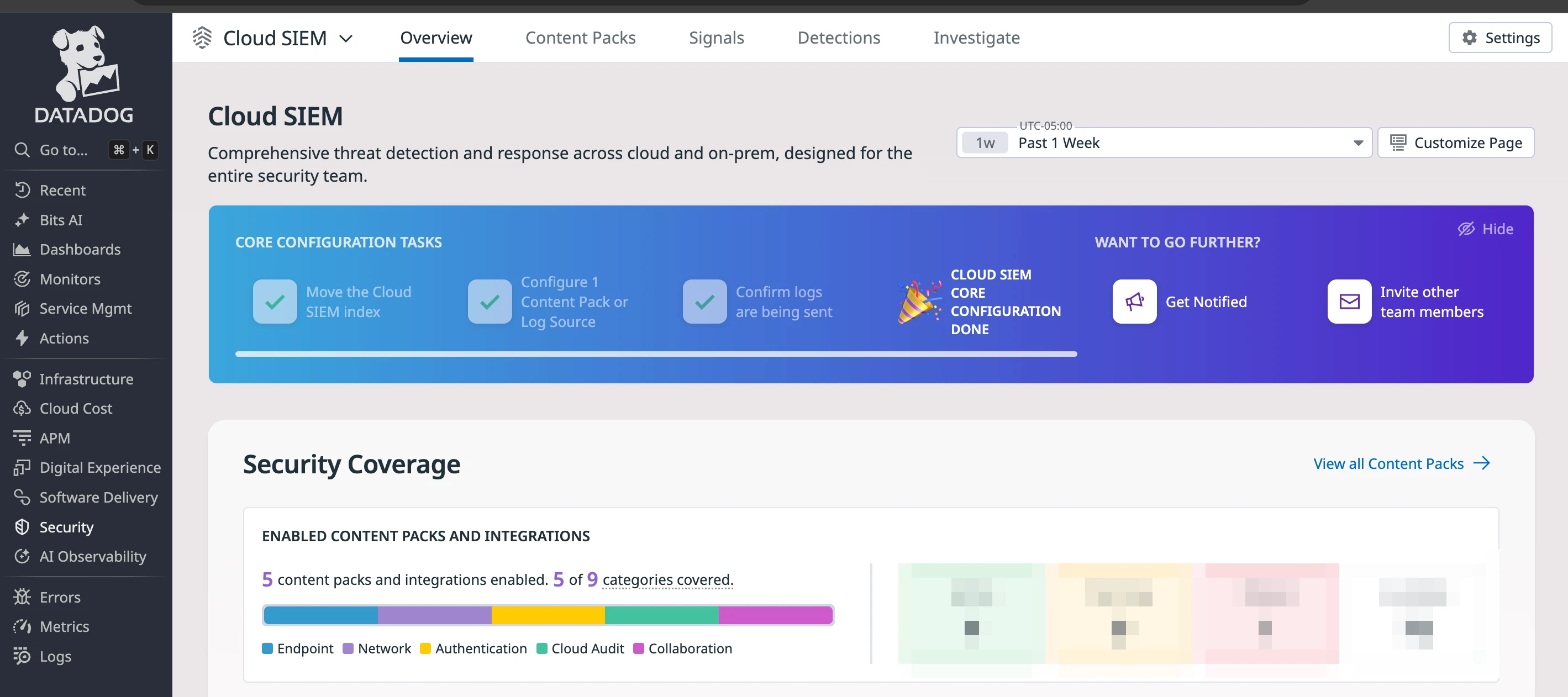
- Machine learning-powered threat detection with continuous analysis
- Integration with the MITRE ATT&CK framework for comprehensive threat coverage
- Real-time correlation of security events across multiple data sources
- Automated alert generation based on predefined and custom security rules
- Centralized security event management and incident response
- Integration with existing security tools
- Comprehensive audit trail and compliance reporting capabilities
Integration benefits: Enhanced Audit Log Capabilities
Endpoints
The Endpoint integration allows you to send MDM Audit Logs to Datadog, providing:
- Mobile device management: Comprehensive audit trails for device configuration changes
- Security policy enforcement: Real-time monitoring of security policy violations
- User activity tracking: Detailed logs of user interactions with managed devices
Collaboration
Datadog's Google Workspace integration gives us the following abilities:
- Identity and access management: Monitor user authentication, authorization, and access patterns
- Administrative actions: Track configuration changes, user management, and policy modifications
- Data loss prevention: Audit file sharing, downloads, and sensitive data access
Cloud Audit
Datadog's Amazon Web Services integration collects logs, events, and most metrics from CloudWatch for several AWS services, delivering:
- Infrastructure security: Monitor AWS resource configurations and access patterns
- Service activity tracking: Comprehensive audit logs for all AWS service interactions
- Cost and resource optimization: Detailed usage analytics and anomaly detection
- Multi-account visibility: Centralized monitoring across multiple AWS accounts
- Automated compliance: Built-in compliance frameworks for various industry standards
Authentication
Datadog's Okta integration provides comprehensive visibility into identity and access management activities:
- Authentication monitoring: Track all user authentication attempts, successful logins, failed attempts, and suspicious authentication patterns
- User lifecycle management: Monitor user provisioning, deprovisioning, role changes, and group membership modifications
- Multi-factor authentication (MFA) tracking: Audit MFA enrollment, usage, and bypass events for security compliance
- Single sign-on (SSO) analytics: Analyze SSO activity across integrated applications and identify access patterns
- Policy and configuration changes: Track administrative changes to authentication policies, password policies, and security settings
- Privileged access monitoring: Enhanced visibility into administrative actions and privileged user behavior
- Anomaly detection: Identify unusual login patterns, impossible travel scenarios, and potential account compromise
- Real-time alerting: Automated notifications for critical security events such as account lockouts, admin privilege escalation, and policy violations
Network
Monitor Cloudflare Web traffic, DNS queries, security threats, and more with enhanced capabilities:
- Web traffic analysis: Detailed insights into web application performance and security
- DNS security monitoring: Real-time analysis of DNS queries and potential threats
- DDoS protection analytics: Comprehensive attack pattern analysis and mitigation tracking
- Zero trust integration: Datadog's out-of-the-box log processing pipeline will automatically parse and normalize your Cloudflare Zero Trust logs
- Content delivery network monitoring: Performance and security analytics for CDN operations