GitHub Actions
Last updated: May 29, 2026
Fluid Attacks provides dedicated GitHub Actions for automated security testing directly in your CI/CD pipeline.
| Action | Scanner | Description |
|---|---|---|
| SAST | Static Application Security Testing | Detects vulnerabilities in your source code |
| SCA | Software Composition Analysis | Detects known CVEs in your dependencies |
| Secret Scan | Secrets Detection | Detects hardcoded credentials and secrets |
| DAST | Dynamic Application Security Testing | Detects vulnerabilities in live web applications |
| CI Gate | Platform integration | Blocks merges when policy-breaking vulnerabilities are present |
How it works
The SAST, SCA, and Secret Scan actions share the same core workflow structure: a checkout step, the scanner action, and an optional SARIF upload to GitHub's Security tab.
Each of these actions automatically switches between full scan and differential scan modes depending on the Git event that triggered the workflow:
- Push to the default branch → full scan of all configured paths.
- Push to a feature branch or pull request → differential scan of only the changed files.
Differential mode keeps CI fast and ensures new vulnerabilities are caught before they reach the default branch.
What it looks like in GitHub
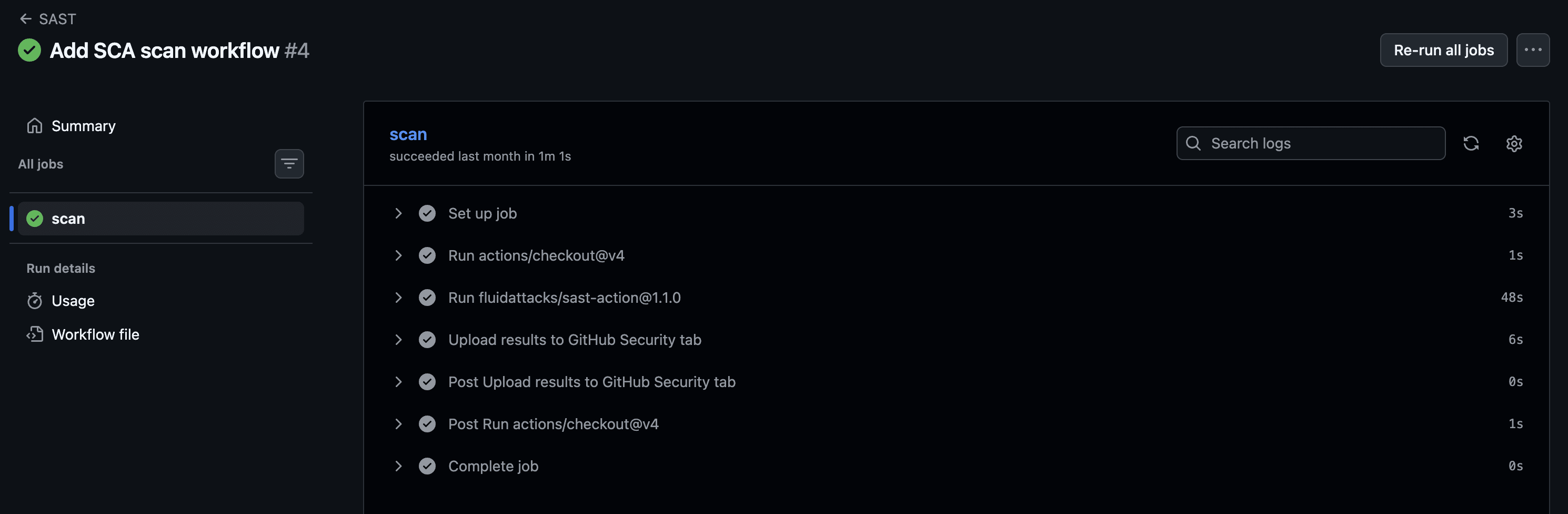
Job steps
After a push or pull request, the workflow appears in the Actions tab with the individual steps: checkout, scan, and upload.
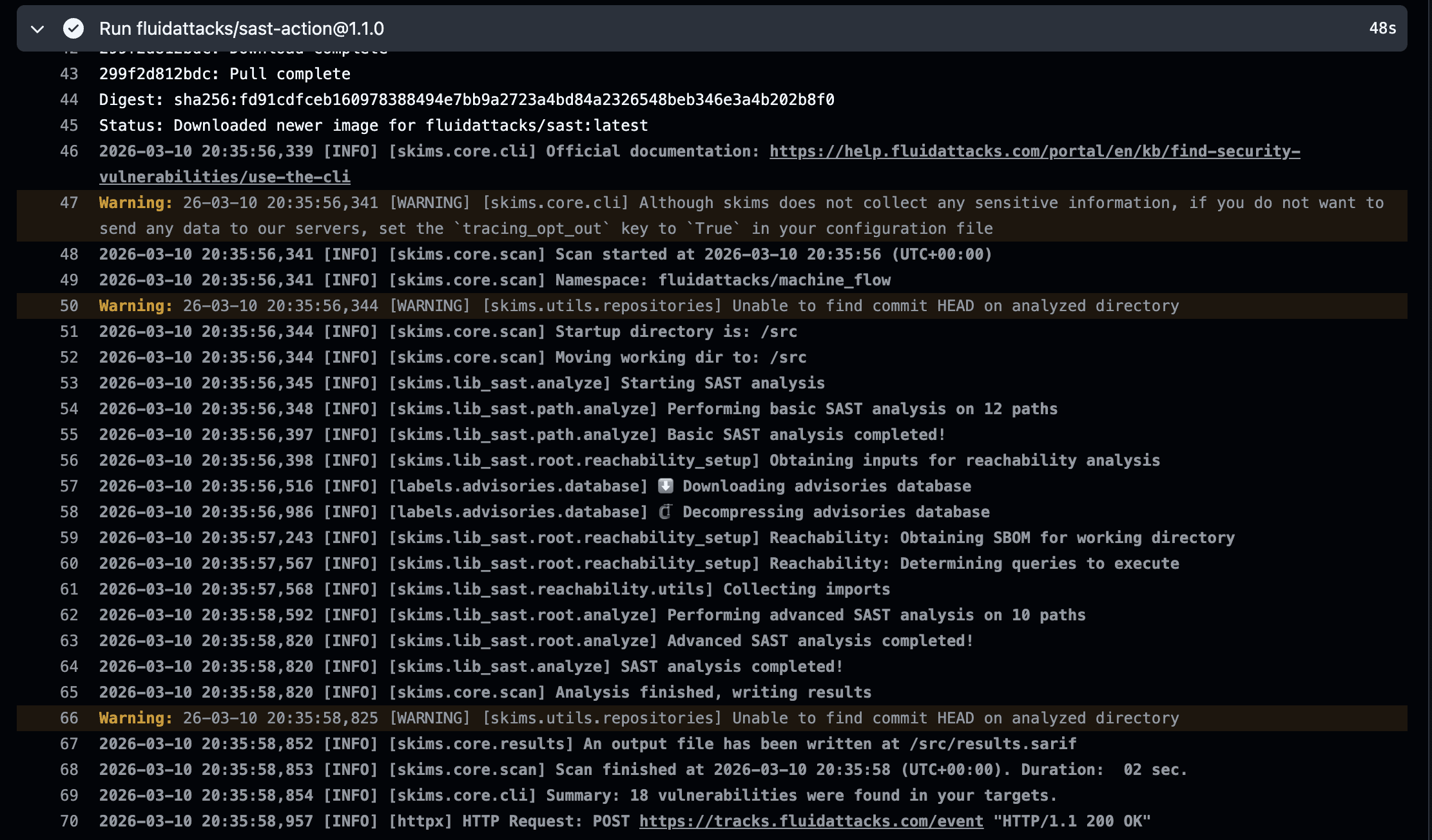
Scanner logs
Expanding the scan step shows the scanner output: which files or dependency manifests were found, what vulnerabilities were detected, and whether the run was a full or differential scan.
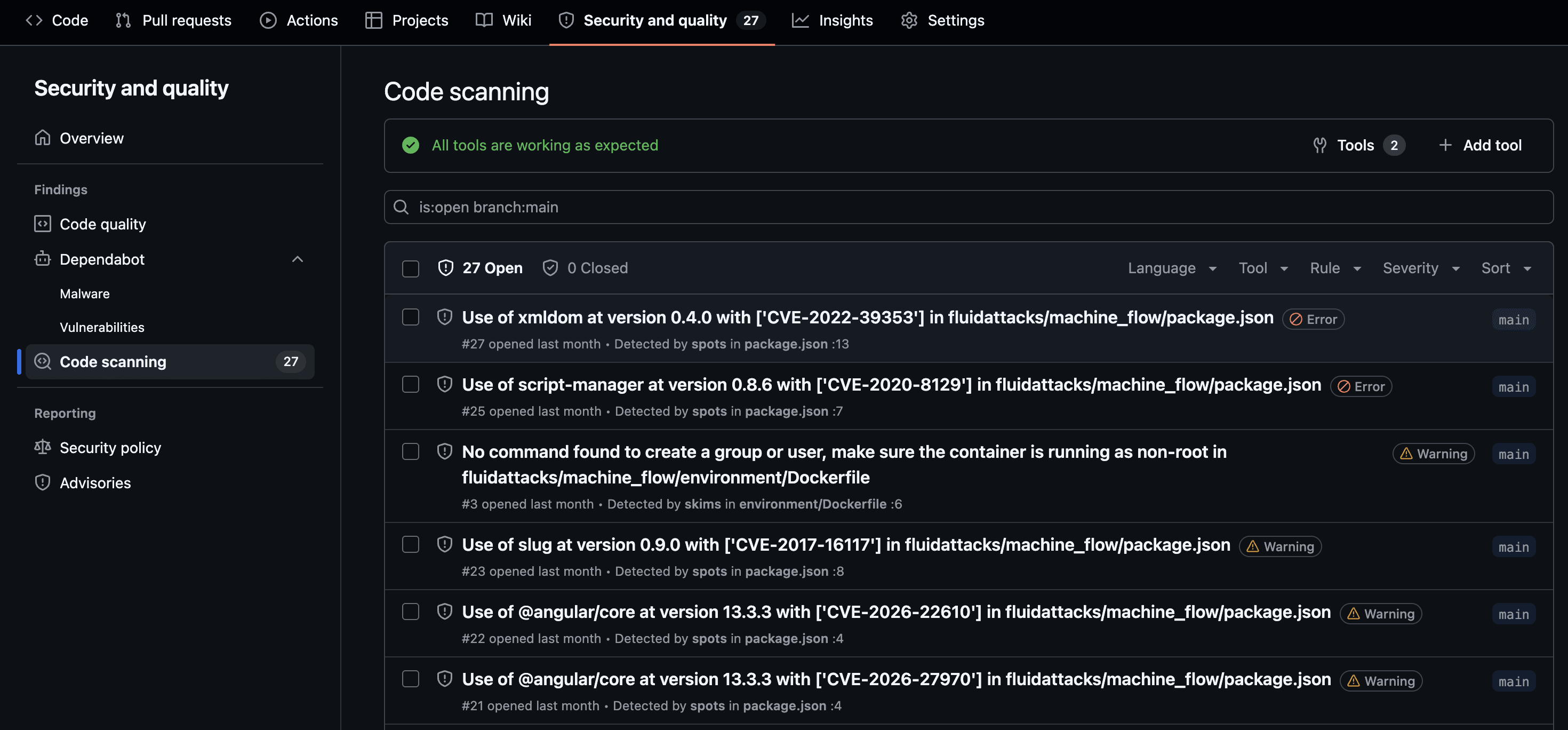
Security tab results
Once the SARIF file is uploaded, findings appear in the repository's Security → Code scanning panel with severity, file location, and a description of each vulnerability.
Privacy: The actions collect only anonymized programming language metadata for analytics. Source code and scan results never leave your runner. See the EULA for details.