Capabilities and use cases
Last updated: May 14, 2026
The Fluid Attacks MCP server exposes 27 tools organized by category. All tools require authentication: Claude Desktop, Claude Code, VS Code, and Windsurf use an OAuth flow with the Fluid Attacks platform, while Cursor authenticates with a Fluid Attacks API token.
(a) Start chats with a mention of Fluid Attacks' API (e.g., "Using Fluid Attacks' API, [...]"), (b) always specify whether your requests are at the group or the organization level, and (c) for requests at the group level, specify the name of the organization as well.
Documentation
Search articles
Tool: search_related_articles
Searches Fluid Attacks' documentation for semantically relevant passages.
When to use:
- Learning about vulnerability types
- Finding remediation guidance
- Understanding security concepts
Example requests:
- "How to configure the SCA scanner to run on Azure DevOps?"
- "What is cross-site scripting?"
Get articles
Tool: get_articles
Fetches full article content from our documentation by article IDs (up to 20 at a time).
When to use:
- Reading full articles found by
search_related_articles - Retrieving detailed documentation on a specific topic
Example requests:
- "Get me the full article on organization policies."
Security scanning
Docker is required to run the scanners. See "Docker installation" for more information.
Run SCA scanner
Tool: run_sca_scanner
Provides instructions to scan your project dependencies for known vulnerabilities.
When to use:
- After adding new dependencies
- Before releasing new versions
- Regular security audits of libraries
Example requests:
- "How do I scan my dependencies?"
- "Run an SCA scan on this project."
- "Check my npm packages for vulnerabilities."
Run SAST scanner
Tool: run_sast_scanner
Provides instructions to scan your source code for security vulnerabilities.
When to use:
- After writing new code
- Before code reviews
- Pre-deployment security checks
Example requests:
- "How do I scan my code for vulnerabilities?"
- "Run a SAST scan on the authentication module."
- "Check my Python code for security issues."
Run both scanners
Tool: run_sca_and_sast_scanners
Provides instructions to run SAST and SCA scans together.
When to use:
- Comprehensive security assessment
- Pre-production security gate
- Weekly security checks
Example requests:
- "Run a complete security scan."
- "Scan both my code and dependencies."
Analytics and reporting
Get organization analytics
Tool: get_organization_analytics
Shows security trends and metrics for your entire organization.
When to use:
- Monthly security reviews
- Executive reporting
- Tracking security improvement over time
Example requests:
- "Show me our ORGANIZATION_NAME's security risk trend for the last quarter."
- "How has our vulnerability count changed over time in the group GROUP_NAME?"
Available document types:
| Document name | Description |
|---|---|
riskOverTimeCvssf | Risk trend using CVSSF scoring |
riskOverTime | Risk trend using raw counts |
distributionOverTimeCvssf | Vulnerability distribution over time (CVSSF) |
distributionOverTime | Vulnerability distribution over time |
assignedVulnerabilitiesCvssf | Assigned vulnerabilities by CVSSF |
assignedVulnerabilities | Assigned vulnerabilities count |
acceptedVulnerabilitiesBySeverity | Accepted vulnerabilities grouped by severity |
acceptedVulnerabilitiesByUser | Accepted vulnerabilities grouped by user |
cvssfBenchmarking | CVSSF benchmarking across groups |
remediatedAcceptedGroup | Remediated vs accepted by group |
Get group analytics
Tool: get_group_analytics
Shows security trends and metrics for a specific group/project.
When to use:
- Project-specific security reviews
- Sprint planning
- Tracking remediation progress
Example requests:
- "Show the security trend for the group GROUP_NAME."
- "How many vulnerabilities were fixed in the group GROUP_NAME this month?"
- "What's the distribution of vulnerabilities in the group GROUP_NAME?"
Available document types: Same as organization analytics, except cvssfBenchmarking and remediatedAcceptedGroup.
Vulnerability management
Find weaknesses in a group
Tool: fetch_group_weaknesses
Lists types of security issues (e.g., SQL Injection, XSS) found in your projects. Supports filtering by status, severity, technique, and location.
When to use:
- Understanding what types of vulnerabilities you have
- Planning targeted security training
- Prioritizing remediation efforts
Example requests:
- "What types of vulnerabilities exist in the group GROUP_NAME?"
- "Show me all critical security weaknesses in the group GROUP_NAME."
Find specific vulnerabilities
Tool: fetch_weakness_vulnerabilities
Lists individual vulnerability instances for a specific weakness with their locations. Supports sorting, filtering by state, treatment, severity, technique, tags, and location.
When to use:
- Assigning fixes to developers
- Tracking specific security issues
- Understanding where problems exist in your code
Example requests:
- "Show me all XSS vulnerabilities in the frontend code repo for the group GROUP_NAME."
- "List untreated vulnerabilities by priority for the group GROUP_NAME."
Get vulnerability details
Tool: get_vulnerability_details
Shows complete information about a specific vulnerability including severity, location, and treatment.
When to use:
- Investigating a security issue
- Understanding how to fix a vulnerability
- Reviewing a vulnerability before closing it
Example requests:
- "Show me details for vulnerability VULNERABILITY_UUID."
- "What's the full information on the SQL injection in login.py for the group GROUP_NAME?"
Get fix metadata
Tool: get_fix_metadata
Retrieves technology-specific remediation guidance for a specific vulnerability.
When to use:
- Getting actionable fix instructions for a vulnerability
- Understanding what code changes are needed
Example requests:
- "How do I fix vulnerability VULNERABILITY_UUID?"
Get a vulnerability report
Tool: get_group_weaknesses_report
Creates a summarized report of weaknesses grouped by vulnerability type. Supports filtering by title, state, severity, technique, and location.
When to use:
- Security audits
- Compliance reporting
- Sprint planning meetings
- Management presentations
Example requests:
- "Generate a vulnerability report for the ProductionAPI group."
- "Show me a report of all open security issues in the group GROUP_NAME."
- "Create a summary of vulnerabilities by severity in the group GROUP_NAME."
Get a vulnerability overview
Tool: get_group_weaknesses_overview
Shows counts of vulnerabilities and weaknesses at a glance.
When to use:
- Quick daily status checks
- Dashboard creation
- Priority assessment
Example requests:
- "How many open vulnerabilities do we have in the group GROUP_NAME?"
- "Give me a vulnerability count summary for the group GROUP_NAME."
Get vulnerabilities by root
Tool: fetch_group_root_vulnerabilities
Shows vulnerabilities found in a specific repository, IP, or URL. Supports filtering by state, severity, and technique.
When to use:
- Repository-specific security review
- Assigning work to teams responsible for specific assets
- Understanding security issues in one part of your infrastructure
Example requests:
- "What vulnerabilities are in the main-app repository?"
- "Show me security issues for the production URL."
Asset discovery
View Git repositories
Tool: get_group_git_roots
Lists source code repositories being tested for security. Supports filtering by nickname, state (active/inactive), and search.
When to use:
- Verifying what code is being scanned
- Finding specific repositories
- Ensuring all code is covered
Example requests:
- "What Git repositories are we testing?"
- "Show me all code repositories for the group GROUP_NAME."
View IP addresses
Tool: get_group_ip_roots
Lists applications and services accessible via IP addresses being tested.
When to use:
- Black-box testing scope verification
- Network security assessment
Example requests:
- "What IP addresses are we scanning?"
- "Show me all tested network endpoints."
View URLs
Tool: get_group_url_roots
Lists live websites and web applications being tested.
When to use:
- Verifying production testing scope
- Web application security assessment
Example requests:
- "What websites are we testing?"
- "Show me all URLs for the E-commerce project."
Organization and group management
List organization groups
Tool: get_organization_groups
Lists all groups within an organization.
Example requests:
- "What groups are in the ORGANIZATION_NAME organization?"
Get organization groups information
Tool: get_organization_groups_information
Gets detailed group information including weakness and vulnerability counts.
Example requests:
- "Show me a summary of all groups in ORGANIZATION_NAME."
Get group information
Tool: get_group_information
Gets group details including description, language, service level, and managed status.
Example requests:
- "What's the configuration of the group GROUP_NAME?"
Get group remediation information
Tool: get_group_remediation_information
Gets remediation metrics including mean time to remediate and remediation rate.
Example requests:
- "What's the remediation rate for the group GROUP_NAME?"
DevSecOps integration
View CI/CD security results
Tool: get_devsecops_agent_executions
Shows results from automated security scans in your development pipeline.
When to use:
- Checking build status
- Investigating failed security gates
- Monitoring automation effectiveness
Example requests:
- "How many builds failed security checks this week for the group GROUP_NAME?"
- "What was the result of the last Forces execution for the group GROUP_NAME?"
View unsolved events
Tool: get_unsolved_events
Lists security incidents and situations requiring attention.
When to use:
- Daily incident review
- Security event management
- Prioritizing urgent issues
Example requests:
- "What security events need my attention?"
- "Show me unsolved incidents."
Platform navigation
Execute GraphQL queries
Tool: query
Executes arbitrary read-only GraphQL queries against the Fluid Attacks API. Mutations are not supported.
When to use:
- Querying data not covered by other tools
- Advanced or custom queries
Describe GraphQL types
Tool: describe_graphql_type
Introspects the GraphQL schema to discover available types, fields, and arguments.
When to use:
- Exploring the API schema before writing queries
- Understanding available fields for a type
Get user info
Tool: get_user_info
Gets information about the current authenticated user including role, organizations, and groups.
Identify repository context
Tool: identify_repository_context
Maps a repository URL or nickname to its corresponding Fluid Attacks group and root.
When to use:
- Identifying which group a repository belongs to
- Setting up context for further queries
Specialized prompts
The MCP server includes specialized prompts designed to help AI agents perform security-related tasks.
run_sca
Pass the instructions to run the SCA scanner to the LLM.
Usage: /fluidattacks-mcp/run_sca
run_sast
Pass the instructions to run the SAST scanner to the LLM.
Usage: /fluidattacks-mcp/run_sast
run_sca_and_sast
Pass the instructions to run the SCA and SAST scanners to the LLM.
Usage: /fluidattacks-mcp/run_sca_and_sast
get_technology_based_remediation_strategy
Pass the technology-specific remediation guidance to the LLM.
Usage: /fluidattacksmcp/get_technology_based_remediation_strategy
configure_github_sca_integration
Pass the instructions to configure the SCA scanner to run on GitHub Actions to the LLM.
Usage: /fluidattacks-mcp/configure_github_sca_integration
configure_github_sast_integration
Pass the instructions to configure the SAST scanner to run on GitHub Actions to the LLM.
Usage: /fluidattacks-mcp/configure_github_sast_integration
configure_agents_md
Configure the AGENTS.md file in the project root directory.
Usage: /fluidattacks-mcp/config_agents_md
How to use these prompts
To use Fluid Attacks MCP prompts,
you start by typing the command name in the chat of your AI agent.
For example,
to configure the AGENTS.md file,
you would type: /fluidattacks-mcp/config_agents_md
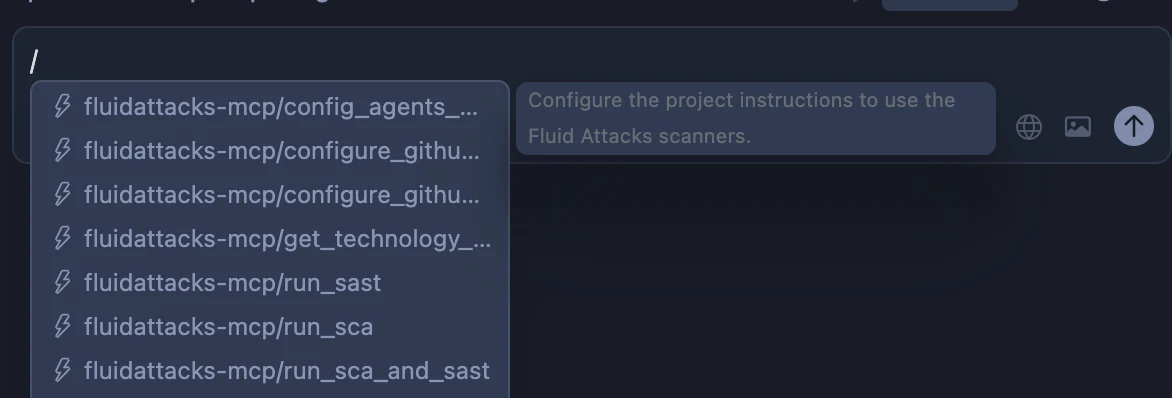
Select the command you want to use and press Enter.
Have an idea to simplify our architecture, or noticed docs that could use some love? Don't hesitate to open an issue or submit improvements.
Installation
Integrate the Fluid Attacks MCP server to use natural language queries in AI tools (examples in Claude, Cursor, VS Code, and Windsurf). Also, integrate our scanners into your SDLC using AI agents.
Docker installation
Install Docker Desktop to run security scans through the Fluid Attacks MCP server in your IDE or AI coding assistant.