App help options
Last updated: Apr 14, 2026
Have you already got the Jira integration? If not, install it.
Access the link in issues to request a Talk to a Pentester session
Permission required: In order to access the link in
Jira issues to request
Talk to a Pentester
sessions, you must have permission to assign or be assigned issues.
Plan required: Advanced
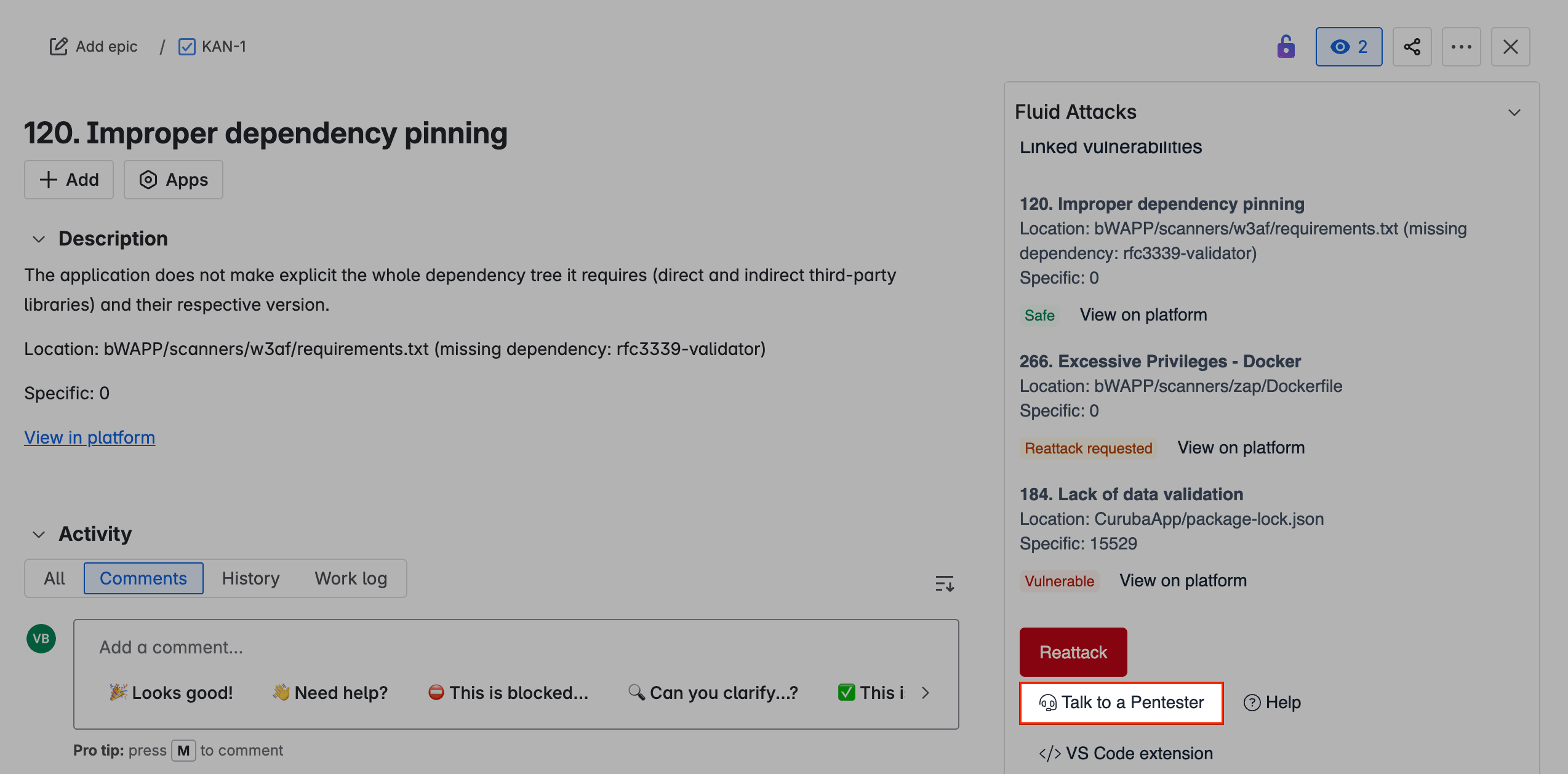
As a user of Fluid Attacks' Jira integration, you can access Fluid Attacks' Talk to a Pentester option without leaving Jira.
This help option is present and enabled in every issue linked to a vulnerability reported by Fluid Attacks. To find it, follow these steps:
-
In your Jira Cloud instance, open the project where you need help with a vulnerability reported by Fluid Attacks.
-
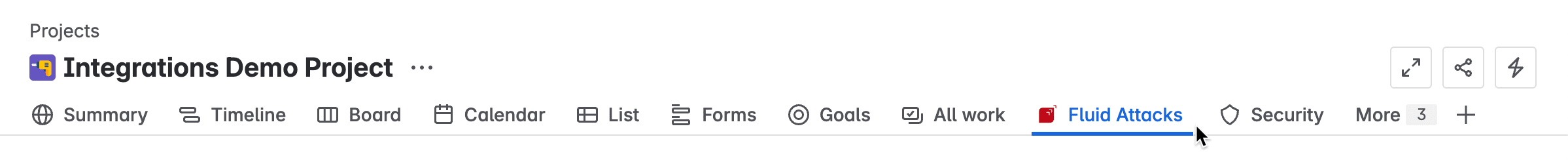
Access Fluid Attacks from the project menu.
-
Find the issue linked to the vulnerability and open it by clicking on View.
-
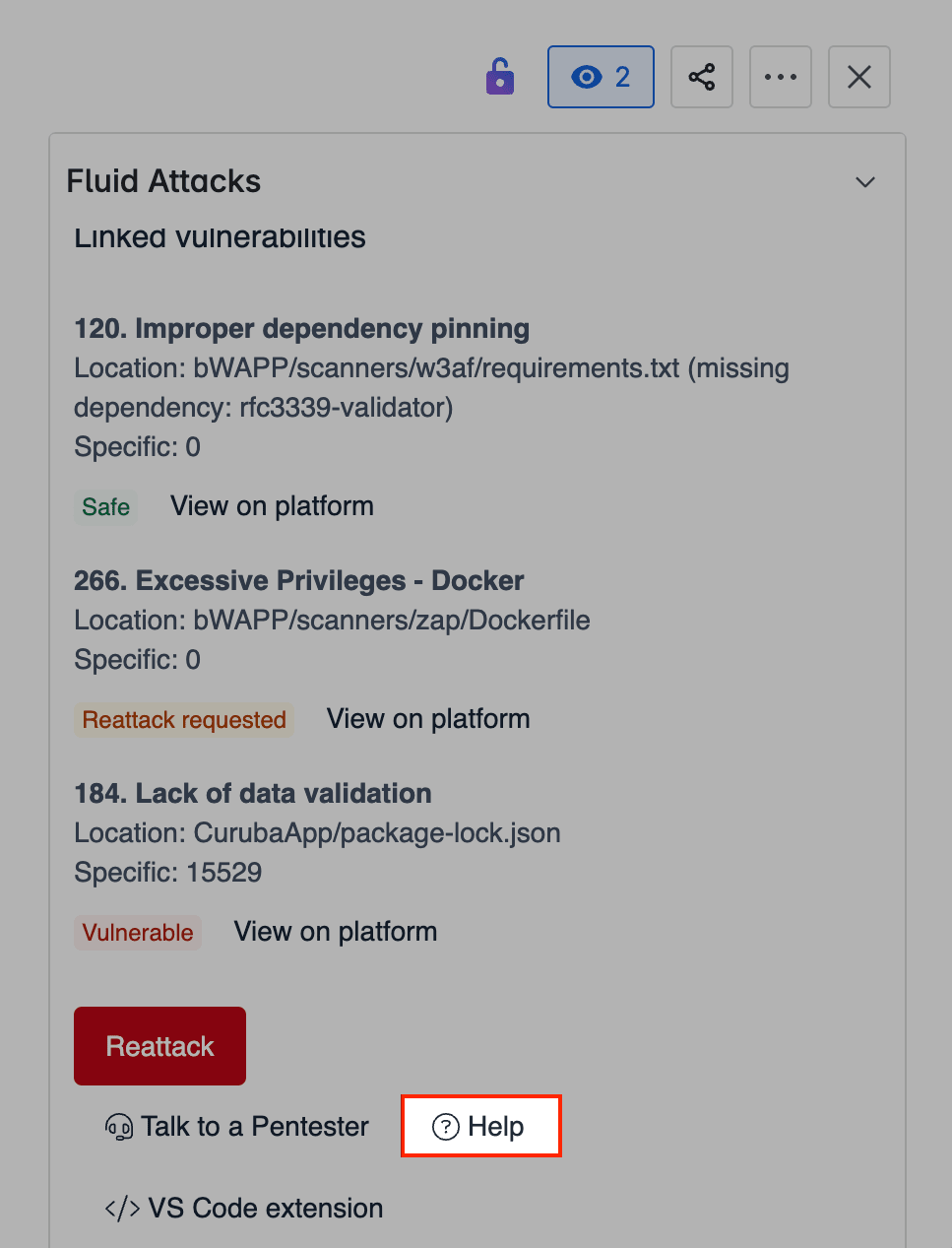
On the right, scroll down to the option Talk to a Pentester.
-
In the Calendly page, follow the prompts to schedule your session.
Access the link in issues to create a help ticket
Permission required: In order to access the link in Jira issues to create help tickets for Fluid Attacks, you must have permission to assign or be assigned Jira issues.
Thanks to Fluid Attacks' Jira integration, you can find a link on Jira issues to access the Fluid Attacks ticket system. There, you can send Fluid Attacks tickets about bugs, requests or questions.
-
In your Jira Cloud instance, open the project where you need help from Fluid Attacks.
-
Access Fluid Attacks from the project menu.
-
Find the issue related to the bug, request or question and open it.
-
Scroll down to the Fluid Attacks options and select Help.
-
Provide the information on the ticket platform and click Submit when you are done.
Search for vulnerabilities in your apps for free with Fluid Attacks' automated security testing! Start your 21-day free trial and discover the benefits of the Continuous Hacking Essential plan. If you prefer the Advanced plan, which includes the expertise of Fluid Attacks' hacking team, fill out this contact form.