Groups section
Last updated: Apr 10, 2026
Groups correspond to independent management units created by you within your organization on the Fluid Attacks platform, consisting of one or more repositories and environments of the evaluated system, from which vulnerabilities are reported. Therefore, you may have several groups, and this is the recommended action, implying independent access, reports, tracking of vulnerability management, and policies (read the details in our FAQ).
When you create a group, Fluid Attacks' multi-method vulnerability scanner starts assessing the system associated with it in search of vulnerabilities. Moreover, if you are subscribed to the Advanced plan, Fluid Attacks' team of pentesters also assesses your system.
The platform has a Groups section, which is described in detail below.
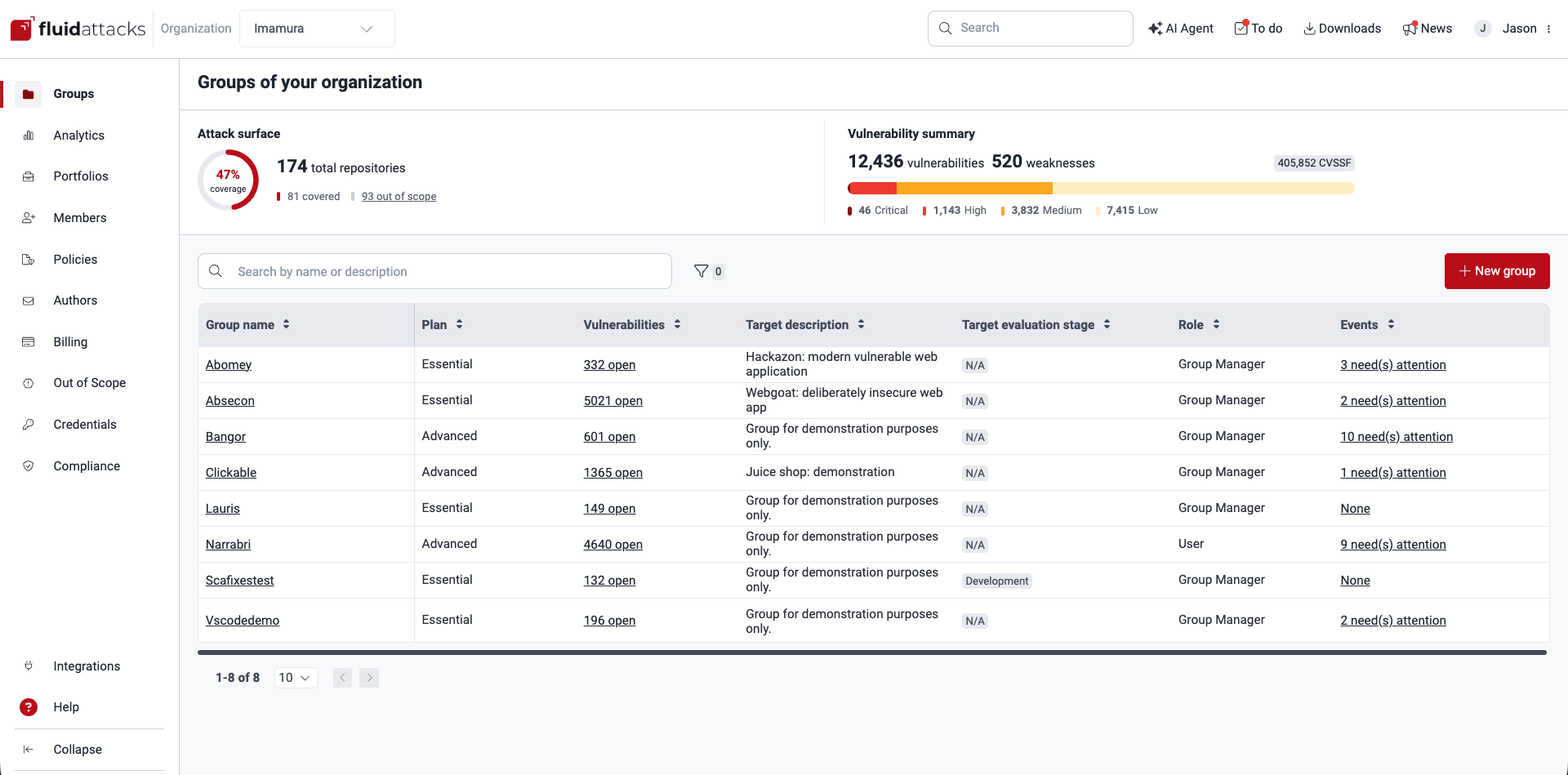
Attack surface
In the upper part of Groups, you can see how much of your attack surface is covered by Fluid Attacks' tests. Here is a description of the information:
- [#]% coverage: The percentage of your repositories retrieved by Fluid Attacks through OAuth which are already in a group and therefore within scope of security tests
- [#] total repositories: The number of your repositories retrieved
- [#] covered: The number of your repositories retrieved and already in a group
- [#] out of scope: The number of your repositories retrieved which need to be assigned a group (click on the link to manage this in the Out of scope section)
All members of your organization are shown the same information regardless of their having access or not to all the groups within it.
Vulnerability summary
Also in the upper part of Groups, you can see a high-level summary of vulnerability findings across the groups in your organization. This is the information shown:
- The number of currently open vulnerabilities
- The number of currently open weaknesses (each weakness is counted as many times as it appears across your groups)
- The total CVSSF units corresponding to open vulnerabilities
- The number of detected vulnerabilities of each CVSS qualitative severity rating
All members of your organization are shown the same information regardless of their having access or not to all the groups within it.
Group table
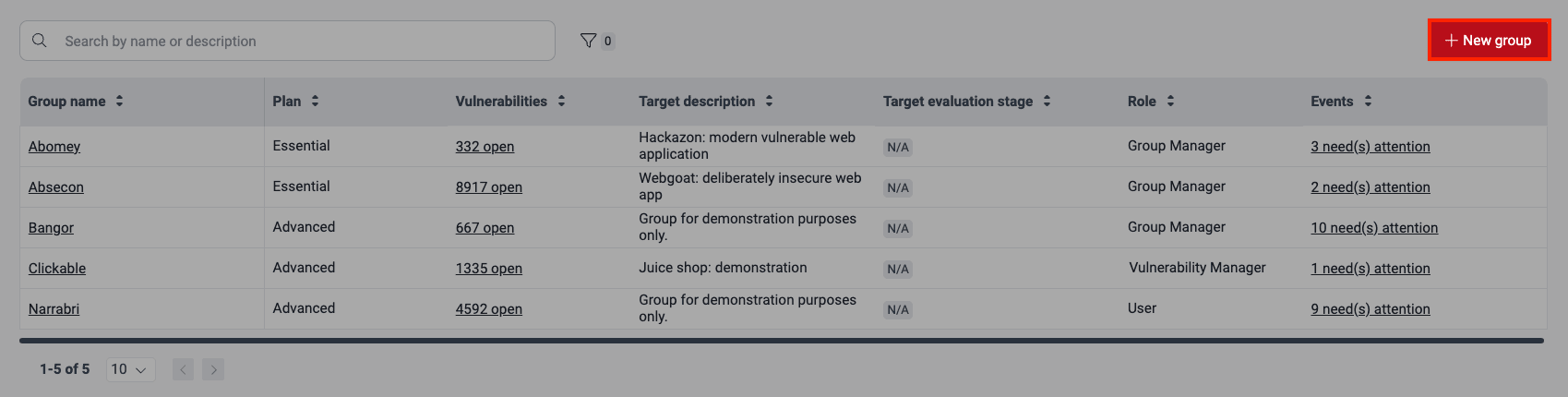
In the group table, you find the names of all the groups you have access to within your organization, along with details about the groups and your role in them. This table has seven columns. You can organize their contents alphabetically or numerically (either in ascending or descending order) by clicking on the arrows next to each column name.
You can filter the table by group name or subscription plan, and you can use the search box to display only the rows that have the content you type in it.

The groups table provides you with the following information:
- Group name: The name your organization has given to the group
- Plan:
Either the plan
to which the group is subscribed
or the indication that the group is assessed under a free trial;
accordingly,
this column may display one of the following values:
- Essential: Secures your application through completely automated security testing and assistance in vulnerability remediation
- Advanced: Leverages the Essential plan features, the manual security testing, and the support in understanding vulnerabilities from a team of pentesters
- Free trial: Secures your application through all the Essential plan features for 21 days
- Vulnerabilities:
Either the total number of open vulnerabilities detected in the system(s)
associated with the group or the status of the assets
provided for the group;
accordingly,
this column may display one of the following values:
- Add repository: The group exists, but a repository to assess has not been added
- Cloning: A repository is being cloned for security testing
- Cloning error: There is an error in the cloning process of all the group's roots
- Testing: A successfully cloned root is being tested
- No vulnerabilities: No vulnerabilities have been found in the system(s) associated with the group
- [#] open: The total number of vulnerabilities detected in the group that have not been remediated
- Target description: A short description of the group given at its creation
- Target evaluation stage:
The kind of environment that will be evaluated,
which can be one of the following:
- Development
- QA
- Pre-production
- Production
- Other (custom environment type)
- Role:
Your role
within the group,
which can be one of the following:
- User: Role for those responsible for understanding and remediating vulnerabilities detected in your software projects
- Vulnerability Manager: Role for those responsible for reviewing the requests of developers (generally with the User role) and tracking progress in remediation
- Group Manager: Role for those responsible for granting access and roles, managing the target of evaluation and policies, and tracking progress in remediation
- Events: The number of unsolved events in the group (i.e., situations that prevent the assessment of part, or the entire, target of evaluation)
You can access sections dedicated to a group by clicking on its name. Your access to the group sections and usage of their available functionalities depend on your role on the platform. You can read a short description of each group-level section on the page "Platform interface and sections".
Create a new group
Role required: Organization Manager
Creating a new group increases the cost of Fluid Attacks' Continuous Hacking, so make sure it is a concerted action within your organization.
To start creating a new group, you need to click on the New group button in the Groups section. Read the page "Create and delete groups" for a detailed description of the steps.
Filter group table data
Role required: User, Vulnerability Manager, Group Manager or Organization Manager
Filters allow you to limit the data you visualize,
facilitating your search.
The Group section has a filter button
(![]() )
which, upon click, allows you to filter the group table
by Events, Plan, Role, Target evaluation stage, and Target type.
)
which, upon click, allows you to filter the group table
by Events, Plan, Role, Target evaluation stage, and Target type.


Any filter applied is shown above the table. And a number next to the filter button indicates the number of applied filters. You can easily clear a filter by clicking on the X next to it.

Search the group table
Role required: User, Vulnerability Manager, Group Manager or Organization Manager
By typing in the search bar in the Groups section, you filter the group table so that the only rows that are shown are those containing the content you type.
See events impeding tests in groups
Role required: User, Vulnerability Manager, Group Manager or Organization Manager
As mentioned above, in the group table, you find a column called Events. These are situations that need your prompt attention to resume the expected course of security testing. In this column, you can discover how many unsolved events need your attention in each of your groups. If you click on this column's contents, you are directed to the Events section of the corresponding group.
Whenever you enter the Groups section and there are unsolved events in one or more groups, a banner appears for a short amount of time. The banner informs of the number of groups that have unsolved events, how many of the latter there are in total, and the number of days since the oldest of those events was reported. By hovering over it, a tooltip appears which tells you the name(s) of the group(s) in question.
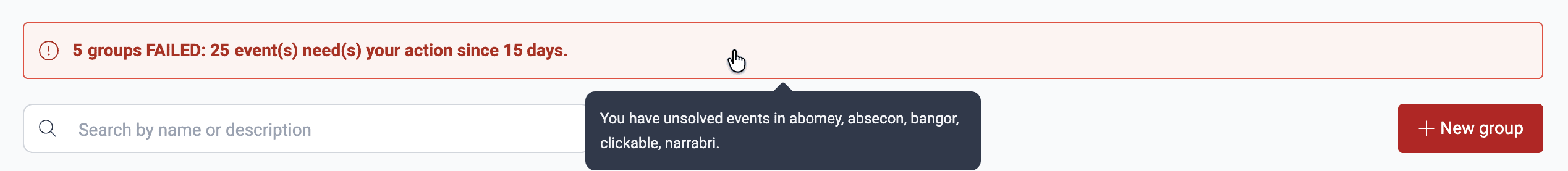
To learn about the types of events and managing them, read the page "Resolve Events impeding tests".
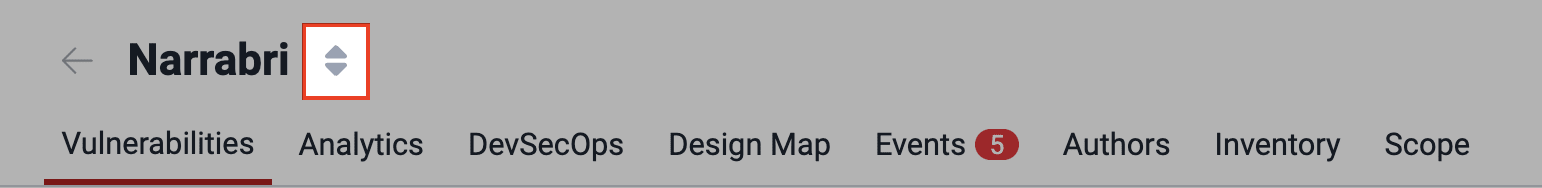
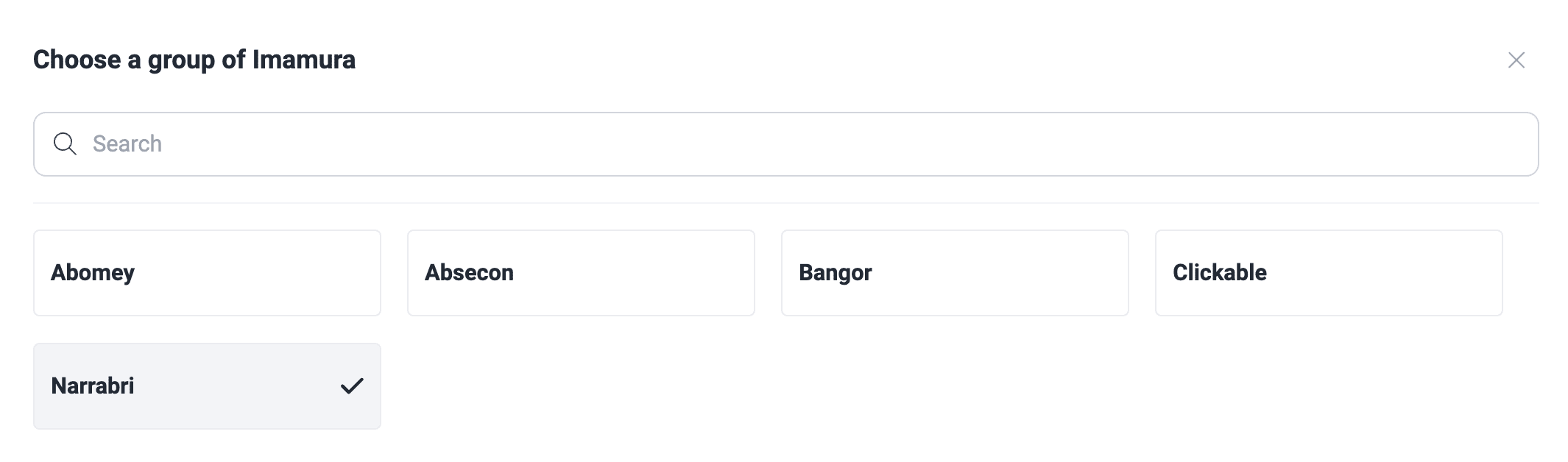
Switch between groups
Once inside a group, to quickly switch to a different group, click on the arrows next to the group's name and choose the group you want to enter from the list.
Search for vulnerabilities in your apps for free with Fluid Attacks' automated security testing! Start your 21-day free trial and discover the benefits of the Continuous Hacking Essential plan. If you prefer the Advanced plan, which includes the expertise of Fluid Attacks' hacking team, fill out this contact form.