Fix code with gen AI from the IDE
Last updated: Mar 16, 2026
After you have learned the details of reported vulnerabilities , Fluid Attacks helps you fix your source code through AI-generated suggestions.
To access Fluid Attacks’ custom guides or automatic fixes produced with generative AI, you need to install and configure Fluid Attacks’ Visual Studio Code extension or Cursor extension . Once you have that covered, come back to these instructions.
Fluid Attacks’ plugin lets you quickly locate the lines of code that need fixing. You can choose to use gen AI to
Follow AI-generated fix guides
The following are the steps to use the plugin’s Custom fix function:
-
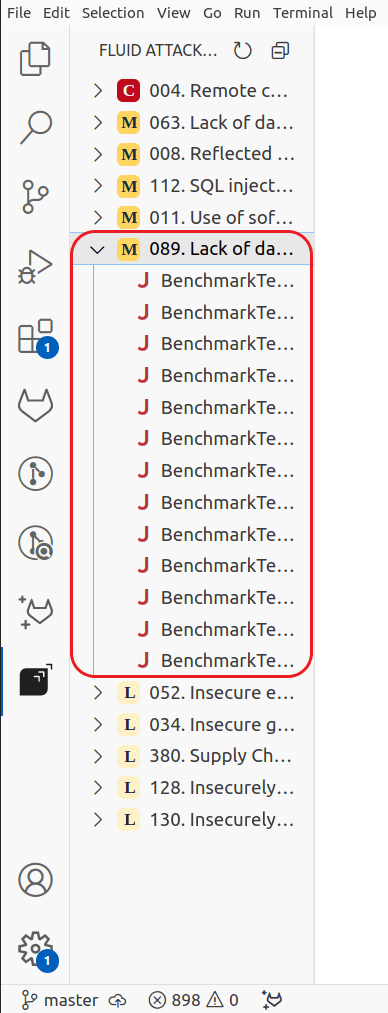
Open the Fluid Attacks extension and click on the type of vulnerability you want to remediate.
-
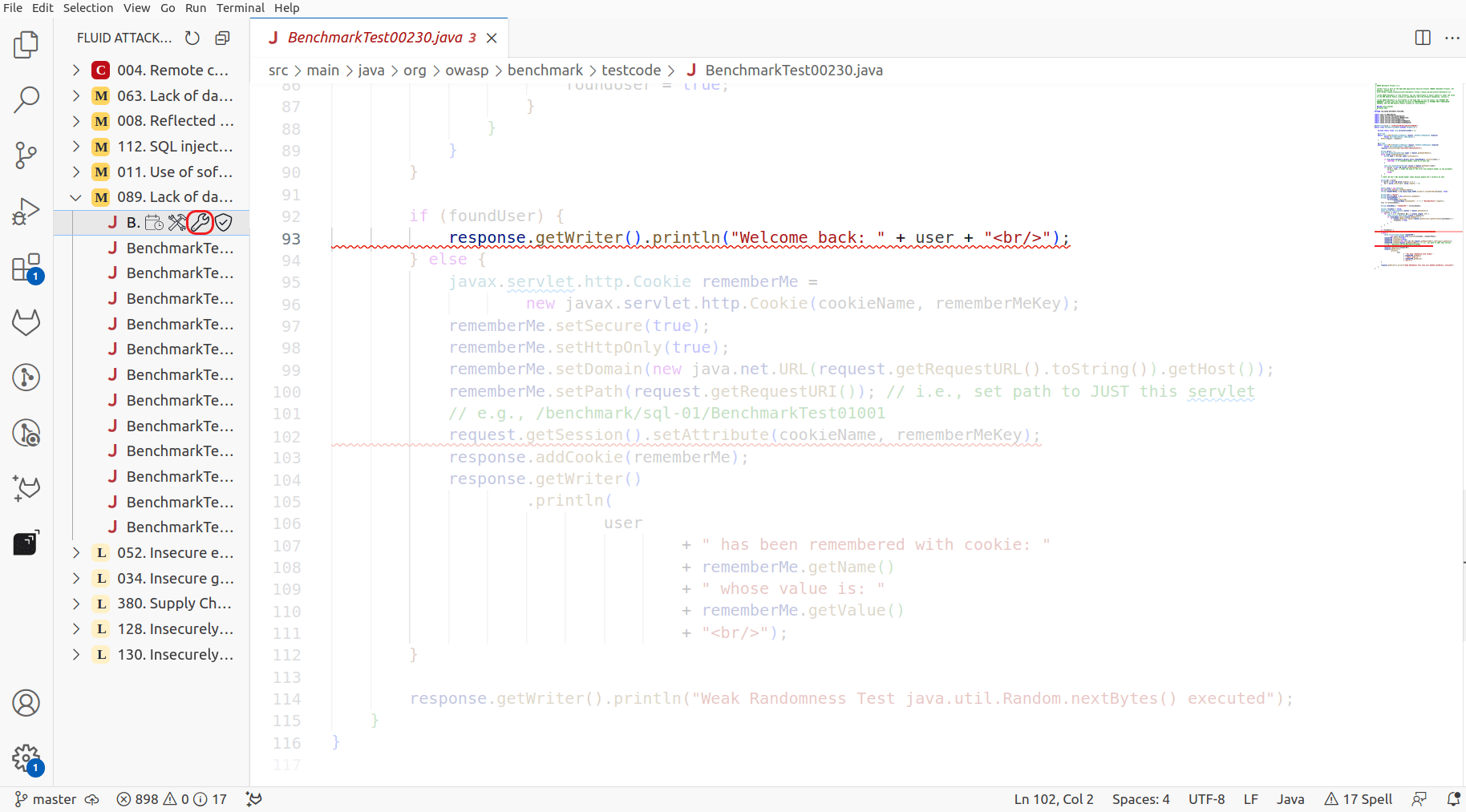
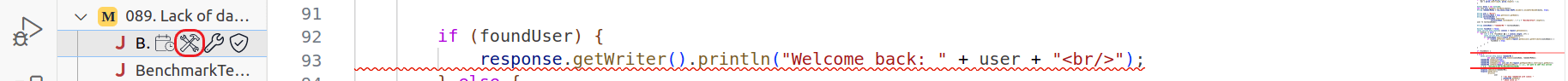
Click the wrench that appears over the entry corresponding to the vulnerable line of code you will fix.
-
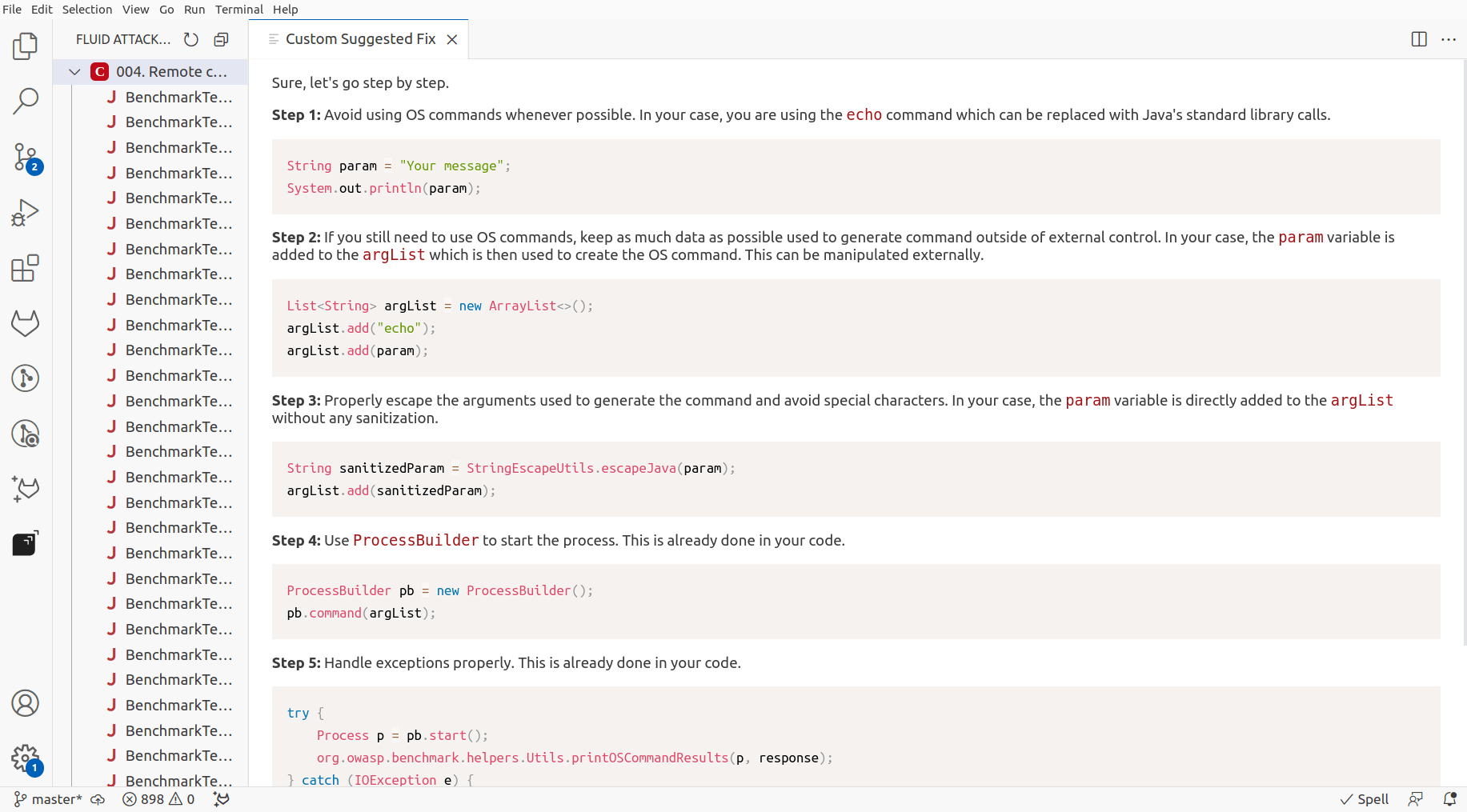
Follow the step-by-step guide to secure your code. Do this critically, as gen AI may produce vulnerable code.
After you have fixed the code, you can verify whether the fix was successful . If you are subscribed to the Advanced plan and need help understanding a vulnerability, you can request an explanatory session with a member of Fluid Attacks’ hacking team.
Get AI-generated automatic fix suggestions
To use the plugin’s Autofix function, do the following:
-
Open the Fluid Attacks extension and click on the type of vulnerability you want to remediate.
-
Click the hammer and wrench appearing over the entry that corresponds to the line of code you wish to fix automatically.
-
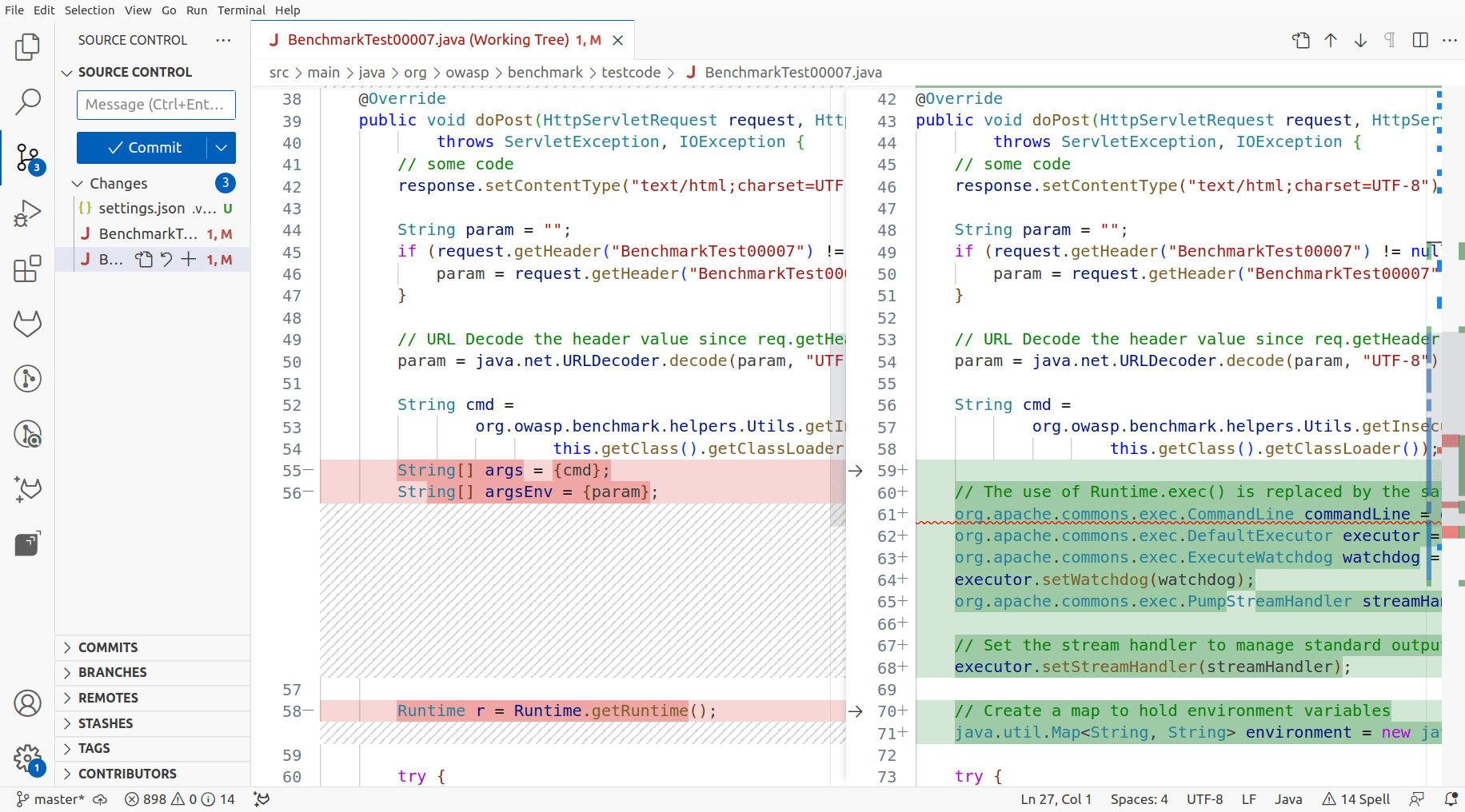
Review the output, which is presented as modifying the file already.
Again, after applying this suggestion, you can request a reattack to verify whether the remediation was successful .